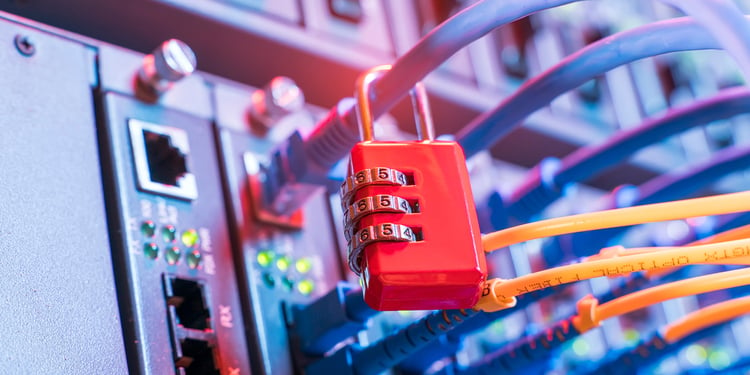
It takes more than 200 days to even detect your system has been hacked, let alone the time you need to fix the damage. The White House has issued an executive order requiring more security at the code level. Brian Gallagher, the US Secret Service vet, is working on a solution that will let you spot an intruder immediately.
Cybersecurity has been an intense battlefield lately. According to Gallagher, the biggest hacks in history have occurred in the last five years and have cost the global economy over $6 trillion annually.
But it goes way beyond economic cost. Recently, a baby's death in Alabama was alleged to be linked with ransomware, following the disruption of access to heart monitors. So it’s a matter of life and death now, too.
Understanding what’s at stake, the Biden’s administration is looking for ways to build new fortifications against devastating cyberattacks by both nation-state actors and money-driven crooks. In May, the Administration issued an Executive Order on Improving Nation’s Cybersecurity, which calls for more security measures at the software code level.
This is what Gallagher is working on. He is now a president and co-founder of ProtectedBy.AI, which developed a solution to detect an intruder instantly and not months after your organization was breached.
CyberNews interviewed Gallagher about some of the most pressing cybersecurity issues and whether it is possible to at least minimize the damage this digital war inflicts upon our daily lives, let alone win it.

There is definitely a lot of news around cybersecurity. What has caught your attention recently?
We've been explicitly focusing on software-related issues. The SolarWinds attack that happened last year kicked us off into looking at issues with supply chain-based attacks and in a way to help clients and customers defend against that specifically. That leads to all of the stuff we are seeing with ransomware right now, both on the corporate and non-corporate side of things, and how attackers are specifically deploying ransomware attacks.
Another area that we are looking at is how cybersecurity can be increased in healthcare specifically. You've seen the reports of the baby that died due to the ransomware attack in the hospital. There's a lot of interest and focus within the community on that specifically and how that may cause changes and policies, procedures, and technology moving forward.
Every report that I get about ransomware and cyber attacks in general points to the increase. Researchers use words like stratospheric when describing the rise in cyber attacks. But I wonder if those attacks are also more sophisticated?
There are new techniques, and the main new technique that has our focus right now is the insertion of malware into the software supply chain, on vendors specifically, in getting software infected at the vendor level and gets pushed out to the end-users. Again, that's what we saw with SolarWinds. When I am talking to people, I tend to equate this to security in 9/11 with the airline industry. Before 9/11, nobody ever thought that criminals and terrorists were going to take over an airplane and crash into a building, so we didn't have procedures in place to protect against that because our minds never thought that was a possibility.
The same thing is true in the cyber world related to supply chain attacks. Before SolarWinds, nobody thought that a criminal or a nation-state would use that type of tactic to affect machines and systems. Once SolarWinds happened, everybody realized this was a new threat, a tactic we now need to prevent. That's why our focus has been in that area for the last six months.
Before SolarWinds, and sometimes now, I used to hear that humans are the weakest element in cybersecurity. But there are so many attack vectors and tactics now, and cybercriminals keep inventing like crazy. It makes me wonder whether we should focus less on people and turn to technology to protect us better?
I'm a firm believer in needing to deploy technology to solve this problem. You are not going to be able to change the habits of every person. Then with the deficiency in cybersecurity professionals - there are over 3,5 million current open cybersecurity positions worldwide, 500,000 in the US alone - you can't just, even on the professional side, throw more people at the problem. The only way to fix this is with tech, and new types of technology get deployed to protect against it.
I think this is part of the problem and where the mind needs to shift. For so many years, organizations have been just focusing on the perimeter of their environment. There are so many different ways to conduct an attack. You can't just focus on the perimeter because the perimeter will get broken, or the threats will be inside the organization, which is where zero trust comes into play. That's precisely why our focus is actually on the software code. That way, when they defeat the perimeter or grandma fails to do what she is supposed to do, we have that protection built into the body of the code itself. And that's the last line of defense. And so we started back at the beginning on how to solve the problem versus just worrying about the perimeter.
What is even the perimeter these days? What do you even need to protect in the context of a hybrid work environment?
This has only gotten worse with COVID and dispersed workforce, people working from home. It has only made it harder for organizations to create more entry points into their networks. A lot of companies will use a VPN, but that's defeatable. You can't just think about your outside walls, and you have to think about the motion detectors within your organization.

So tell me, what solution have you developed recently?
The tool that we build is called CodeLock. It puts these digital signatures into the body of code and uses a blockchain-like structure to monitor for any intrusions into the software. IBM puts out an annual report every year. One of the metrics they are continuously tracking is the average time it takes to detect an insertion attack into an organization. Think about SolarWinds again. The breach was discovered in December, and the attack happened in the first quarter of 2020.
On average, it takes 207 days for an organization to detect that its system has been hacked. And so, the cybercriminal has been in their environment for over 200 days. Because of that length, it takes 76 additional days for them to fix the problem and contain the threat. You are two-thirds away through the year before you even fix the problem. With CodeLock, focused at the software level, we will identify the insertion immediately. Due to our blockchain structure, we will be able to tell the client right wherein the software the insertion occurred to eliminate that delay cycle to address the issue.
We are focused on more enterprise network-level applications and work with those developing software for themselves or their clients. We have customers that are third-party software developers. We work with them and up to government agencies. We are working with the US government right now as well. It's a business-to-business market right now.
You said we should not throw people at the problem. Instead, technology should protect us. When will this become a reality?
I think the industry as a whole is moving that way. You see more automation in the cybersecurity space, applying artificial intelligence, machine learning, robotic process automation. A lot of these are the tools that you are starting to see in that space. Traditional cybersecurity is based on log analysis. Now you have so many logs and so many devices and all of your internet of things pieces, and there's just so much information that people can't analyze and look through it. It's just not practical. Or, if they can, it takes them 200 days to get to it because there's so much information. I think the industry is moving that way now. President Biden signed an executive order in May mandating increased security in software at the code level. That's precisely what we are talking about with CodeLock. I think, by the summer of 2022, you are going to see a shift and a change in thinking about how companies are deploying cybersecurity.
We initially agreed to have this interview when Citizen Lab found the vulnerability in Apple just days before the new iPhone release. The company quickly fixed it. Yet, they didn't talk about security much during their event. They revealed iPhone 13, and it made headlines. Do you think the company was roasted enough in regards to the NSO spying matter?
I think every company is going to be susceptible to an attack. And especially if you are Apple or Facebook, or Samsung, any of these bigger players. They are going to get attacked. Should Apple have been more vocal about things with the users? Probably. But I also understand their perspective of wanting to downplay and minimize the issue. The more significant concern of what happened with NSO Group specifically is just a lack of regulation around those types of companies worldwide. What NSO was doing is nothing new. Governments - the US government, the Israeli government - have had that technology for decades. But the concern with that is who they are using as clients. People may trust the US government more than maybe dictatorships. We have different laws and warrants are required and things that have to be followed to use that type of tech. I think there needs to be more regulation in that space that ultimately protects us as end-users.
What type of regulations are you talking about?
I think the regulation could be sanction-oriented or controlled. From a US perspective, we sure shouldn't allow companies like NSO to sell that military-grade technology to nation-states that we would consider unfriendly or against our diplomatic goals.
The fact that NSO was a private company targeting another company, in essence, that's industrial espionage. That shouldn't be legal or allowed. Just because NSO found a loophole in their software, the theft of the data was theft. That's wrong. I think the laws need to be strengthened to support that.
Do you think it will happen? Cybersecurity seems to be in the spotlight under Biden's administration.
To be fair, the last administration put a bunch of cyber legislation in place as well. Still, the Biden administration has picked that up because they have been dealing with the vast majority of attacks over the last six to eight months. I do think that it is going to change.
I was a little disappointed at the length of time from the last executive order; I think (the government) needs to respond faster - they had this in their court for the last year; they need to enforce action.
I believe that changes are going to come, but it will take longer than I think it should.
More from CyberNews:
Threat actor leaks Mercedes-Benz platform’s source code
Why do cyber gangs win? Because 'bad guys' talk to each other - interview
Cybersecurity professionals’ salaries disclosed: North Americans earn $119,000
Scammers are sending fake emails about Economic Impact Payments
Should you worry? 100 countries ranked by cyber safety
Subscribe to our newsletter





Your email address will not be published. Required fields are markedmarked