
A user on a popular hacking forum is selling a database that purportedly contains more than 257,000 user records from orakulas.lt (now known as Olybet.lt), a Lithuanian online betting service. Olybet is part of Olympic Entertainment Group, which is in turn owned by private equity firm Novalpina Holding group.
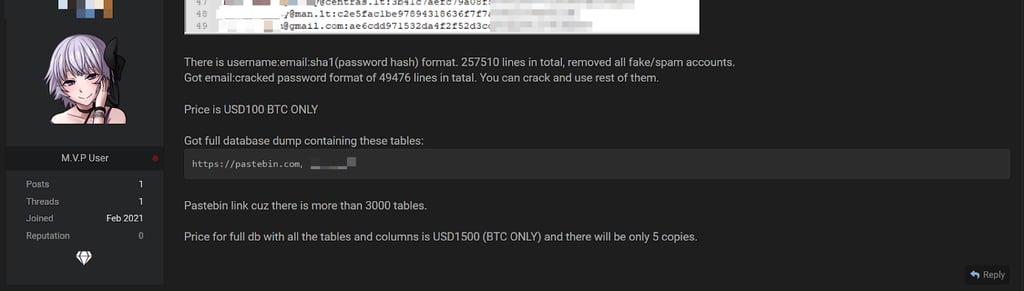
The forum user is selling the login details - email addresses and hashed passwords - of 257,510 orakulas.lt accounts for $100 in bitcoin. At the same, five copies of another archive potentially containing 3,087 tables that might include much more sensitive personal data such as passports, ID card scans, and credit card details of more than a quarter-million users, are being sold by the same threat actor for $1500 in bitcoin.
Use our personal data leak checker now to see if your email address has been exposed in previous leaks.
Example of user data put for sale as seen in the screenshot on the hacker forum:

To confirm whether the database was genuine and whether Olybet was aware of any breaches to their systems, we reached out to Tomas Palevičius, General Manager of Olympic Casino Group Baltic.
Palevičius confirmed that the database seems to have belonged to orakulas.lt, which was bought by Olybet and rebranded as olybet.lt in 2015. According to him, Olybet operates under a different license than orakulas.lt and the databases used by Olybet are of a different nature.
Palevičius stated that Olybet was not aware of any data leaks following the rebrand from orakulas.lt. The company’s security specialists, who are currently conducting an internal investigation into the incident, have examined the entries included in the threat actor’s screenshot and have not found any of the breached accounts in Olybet databases, Palevičius said.
What was leaked?
Based on the samples we saw from the archive that is being sold for $100, it contains user email addresses and passwords that have been hashed using the weak SHA1 algorithm, which can be cracked by cybercriminals without too much effort.
The threat actor claims to have cracked 49,476 out of 257,510 passwords, with the rest still unbreached before the database was put up for sale.
The author of the forum post claims that the second part of the database allegedly contains 3,087 tables that include a wide variety of deeply sensitive personal and service-related data of orakulas.lt users, such as:
- Document scans
- Credit card details
- Personal messages
- Bank account details
- Transaction data
Example of data tables contained in the second orakulas.lt archive:

By investigating the screenshots of the database posted online by the threat actor, we can see that the table begins with email addresses containing old and obsolete email domains, many of which are no longer used by Lithuanian users. With that being said, we cannot determine the age of the database with absolute certainty because those are merely the first entries in the table.
That, and the fact that the very first user account belongs to the administrator of orakulas.lt, might indicate that these older email addresses belonged to the users who were the first to sign up for the online betting service, which would be consistent with the email domains listed in the screenshot. This means that there is a possibility that newer user records are present in the database.
Stay tuned for more information
Our investigation of the leak is ongoing, and we will update the story as it unfolds.
In the meantime, consider using our personal data leak checker with a library of 15+ billion breached accounts to find out if any of your online accounts have been leaked in previous breaches.






Your email address will not be published. Required fields are markedmarked