
Digital surveillance of journalists and human rights activists is on the rise. Following the widely reported leaks of various confidential papers, such as the PANDORA papers and WikiLeaks, governments worldwide have become more active in monitoring journalists' communications to prevent potential leaks and, consequently, the embarrassment of revealing sensitive government secrets to the public.
The advancement of digital technologies has shifted most communications to digital platforms. For instance, modern journalists now use internet messaging applications (e.g. WhatsApp, Telegram, and Signal) to exchange messages and files and to communicate with their sources. Governments employ advanced spyware to monitor communications on computers and smartphones. The deployment of digital surveillance tools has resulted in the arrest and even killing of many journalists worldwide.
One of the most famous examples of using spyware to monitor journalists and other civilian activists was the Pegasus spyware incident. In the summer of 2021, world news revealed the use of the Pegasus spyware – which was developed by the Israeli cyber-intelligence firm NSO Group Technologies – by various governments around the world to monitor human rights activists, journalists, and political figures. Although the spyware was initially developed as an anti-terrorist measure, the leak of more than 50,000 phone numbers targeted for surveillance by Pegasus' customers to Amnesty International and Forbidden Stories shows that governments greatly abused the tool for other purposes.
In this article, I'll discuss how government agencies can install spyware on targeted individuals' computing devices, give some examples of similar incidents, and conclude with technical advice to mitigate this risk.
How can spyware be installed on a journalist's phone without them noticing it?
There are numerous ways in which threat actors can install monitoring tools on end-users' devices. The following lists the most common methods:
- Malicious applications: Threat actors could abuse popular applications and download websites (e.g., Google Play, Samsung Galaxy Store, and Apple Store) to spread spyware. For example, a recent attack discovered by ESET researchers found that the Chinese APT group GREF uploaded trojanized apps (Telegram and Signal) into the Google Play store and Samsung Galaxy Store. The attack aims to spy on smartphones of the Uyghur ethnic minority outside of China.
- Phishing emails: Sending spearphishing emails is the preferred method to install spyware silently on target smartphones and computers. Phishing attacks can occur via different methods, including internet messaging apps and social media platforms like Facebook Messenger, in addition to SMS. The infamous Pegasus spyware used a spearphishing attack via emails and SMS text messages to infect its targets. Once installed on the victim's smartphone (support installation on Android and iPhone), it will turn into a 24-hour surveillance device.
- Drive-by downloads: In this technique, threat actors utilize compromised websites hosting exploit kits that target and exploit security vulnerabilities in a user's browser or apps when they visit. If successful, the exploit kit will silently download spyware payloads onto the end user's system without the user's knowledge.
- Software vulnerabilities: Users' computing devices contain applications in addition to the operating system. Threat actors can exploit security vulnerabilities in applications to install spyware. For example, the Candiru Spyware, which has similar capabilities to the Pegasus spyware, exploits a Google Chrome zero-day flaw (CVE-2022-2294) to install on target devices. Candiru spyware has the ability to record victims' webcam and microphone, keylogging everything they type on their keyboard, exfiltrating messages, browsing history, passwords, and locations in addition to its ability to escalate its privileges by installing a vulnerable signed kernel driver to infect with additional zero-day exploits. The attack was mainly executed against Middle East journalists, especially those living in Lebanon.
- Infected files: Downloading and opening internet files could infect your device with spyware. For instance, threat actors can embed malicious code within MS Office and PDF files to install spyware silently when the user opens the original file.
- Physical access: If attackers successfully gain physical access to your device, they can install spyware through different methods, such as a USB cable or a USB stick. For example, in Juice Jacking, threat actors, especially government agencies, can abuse free USB port charging stations, such as those found in airports and hotels, to infect users with spyware.
- Exploit weaknesses in Wi-Fi and Bluetooth connections: Threat actors can install spyware on target smartphones by exploiting security vulnerabilities existing in old Bluetooth and Wi-Fi protocols to install spyware. For example, in the Dubbed Key Negotiation of Bluetooth (known as KNOB) attacks, threat actors force victim computing devices, such as their smartphone, to use a weak encryption key (1 byte only) when negotiating the connection with other Bluetooth devices. This lets nearby attackers crack the Bluetooth key and intercept communication between the paired devices. Using the same technique, hackers can install spyware on victims' devices.
- Fake updates: Malicious actors can install spyware on victims' devices through deceptive updates. A common example of this attack is when threat actors create a website that closely mimics a legitimate one, such as a popular web browser. When a victim visits the fake website, a pop-up message appears, instructing the victim to download what appears to be the official web browser update. However, the fake update contains hidden malware that stealthily installs itself on the end user's device.
- Pre-installed spyware: In some instances, spyware may already exist on a user's device. For example, a journalist may send their smartphone to a maintenance shop, where spyware is installed without the user's consent. Another scenario involves purchasing a smartphone from a lesser-known company, which could sell products pre-installed with spyware.
The spyware market
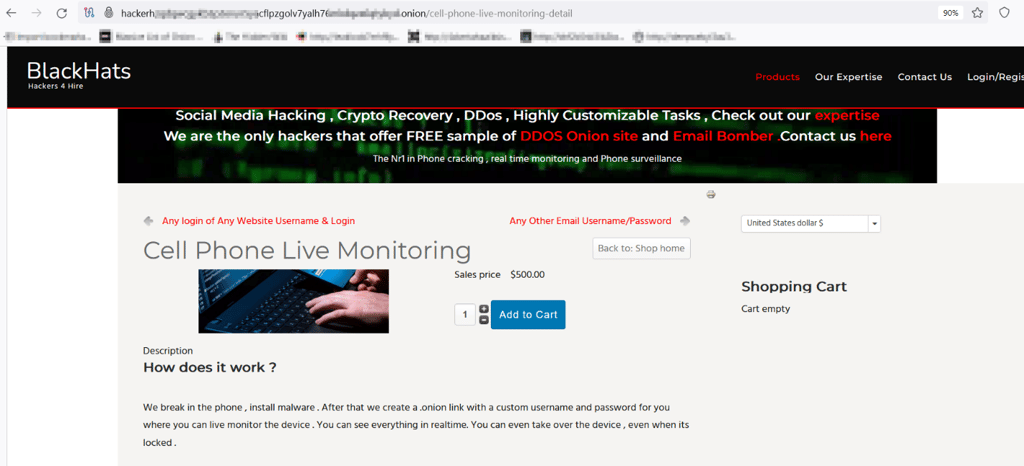
While we may assume that acquiring advanced spyware tools like Pegasus malware is restricted to governments and official agencies, this is not wholly accurate. For instance, even individuals with limited technical expertise can purchase such tools from the darknet or hire hackers to install spying tools on target devices. Some companies advertise selling spying devices on the surface web, but these are typically less efficient than those used by government entities or organized criminal groups and promoted on the darknet, such as the TOR network.
In the TOR darknet, many hackers websites promote selling remote smartphone monitoring services (see Figure 1).
There are many Tech companies selling cell spying tools. These are legitimate companies, and they sell their tools to interested parties to use them legally – such as parental control to monitor your children's smartphones. However, these commercial spying applications can be abused, similar to what happened with the Pegasus spyware, and installed on target devices using any of the delivery methods already discussed. Here is a list of some legitimate spyware applications:
- M spy: allows remote access to all data and monitoring all activities on any phone
- Eyezy: phone monitoring software for parental control
- Cocospy: tracks locations, messages, calls, and apps remotely. Works on Android and iOS smartphones and tablets
How can journalists avoid installing surveillance tools on their computing devices?
Journalists and human rights activists who suspect the installation of malware – such as spyware- on their devices are encouraged to follow the following recommendations:
- Download applications, especially internet messaging apps, from reputable sites only – for example, Google Play for Android and Apple Store for Apple devices
- Keep device operating system up to date
- Enable Two-Factor Authentication (2FA) to protect online accounts
- Install a reputable anti-malware on smartphone devices to remove threats
- Check all mobile applications permissions before installing them
- Do not use public Wi-Fi hotspots to send emails or to chat using IM applications
- Beware of phishing attacks – do not click links on suspicious emails or IM messages sent by anonymous people
- Secure physical access to computing devices and do not allow strangers to access computing devices such as laptops, tablets, workstations, and mobile phones.





Your email address will not be published. Required fields are markedmarked