
A popular chain of convenience stores and gas stations exposed a treasure trove of employee and customer information to the public.
Circle K owner Couche-Tard operates around 14,000 stores worldwide, having sold 12 billion liters of gas this past quarter. In the US, it has around 7,000 branded Circle K stations.
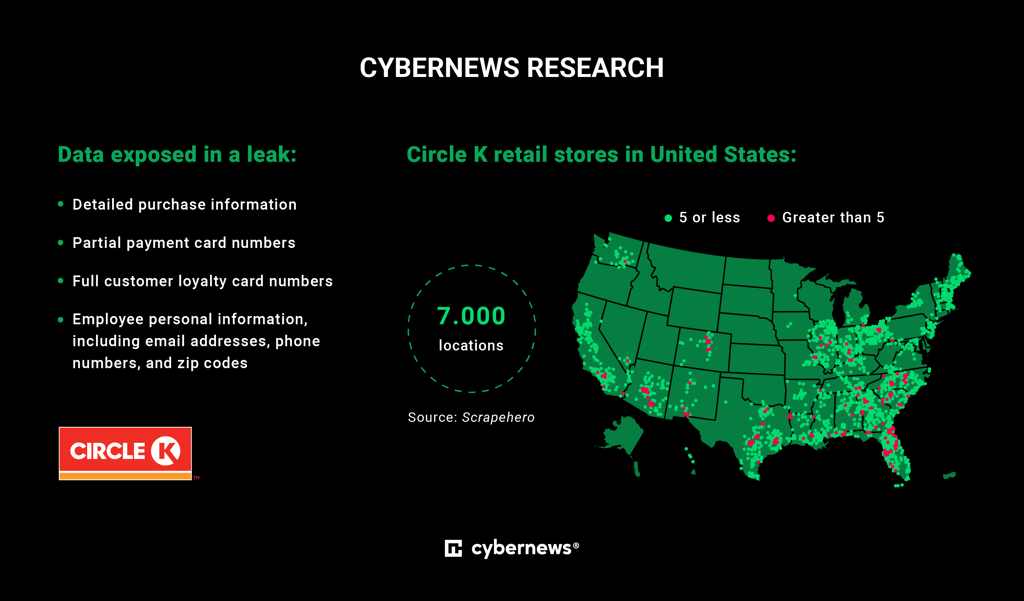
On January 12, 2023, the Cybernews research team discovered an open Circle K US dataset with tons of sensitive information: partial payment card numbers, full customer loyalty card numbers, purchase data, employee email addresses, phone numbers, and zip codes, among other data.
If exploited, the dataset could lead to identity theft, financial fraud, and targeted phishing campaigns, among other criminal activities.
Following our responsible disclosure procedure, we informed the company about the leak, and Circle K immediately fixed the issue, assuring data security was their top priority. The company hasn’t responded to requests for more comprehensive comments on the subject.
Leaking sales data
Cybernews researchers discovered the company’s internal Azure blob storage exposed to the public. Azure blob storage is typically used to create data lakes for analysis and when building cloud-native and mobile apps.
According to Cybernews researchers, the Circle K Azure blob was used to store internal information, such as point of sale (POS) terminal transaction logs and tax, employee, and inventory data.
POS terminals are devices used to process transactions by retail customers. Circle K logged detailed information about purchases, including items, their price, date, and timestamps, full loyalty card numbers, partial credit card numbers, and other transactional data.

The leaked information could provide threat actors with access to customer location and spending habits, and even allow for guessing payment details, which would naturally lead to financial loss.
While Circle K stored only partial credit card information in the format of 511111XXXXXX1234, researchers claim it is still valuable since the first six card numbers point to the card issuer, and the last four digits indicate its owner.
“Having this and other easily accessible information allows one to impersonate a person while calling the bank, verify some transactions and cause financial harm,” researchers said.
With 10 out of 16 card numbers, criminals have to guess only six middle digits, making their task considerably easier.
The dataset also contained full details of loyalty cards. While it is a daily item for many, we overlook its safety, never assuming it could expose our information. In reality, threat actors could exploit that data to map our location and potentially track us.
Treasure trove of employee data
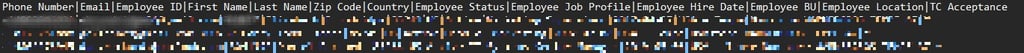
Additionally, our researchers spotted that the open dataset also holds sensitive employee data: full names, personal email addresses, phone numbers, employment status and IDs, ZIP codes, employee hiring date, job title, and working location.
“Leaked employee information could pose a real-life and online danger for those working for the Circle K chain. All personal information could be used in many different criminal activities.”
“Personal accounts could be targeted by phishing campaigns, leading to unauthorized access to internal tools and POS itself. This opens a window for fraudulent activities under employees' names," researchers explained.
They couldn't estimate the size of the leak since it would have required an intrusive scanning of the whole storage blob. However, they noted that the dataset holds all the transactions from the beginning of 2021, with 5000-6000 transaction files logged daily.
How to secure sensitive data
According to the FBI report, over 14,500 convenience stores and nearly 8,000 gas stations were robbed in 2021 alone, making them one of the top targets for crooks. Leaving sensitive employee data out in the open would make their job easier.
Therefore, protecting any open dataset is crucial for every organization. As for Azure storage blobs, Microsoft has listed several security recommendations.
Every online instance should be treated as public and secured with no shortcuts. Extra effort is required whenever a dataset contains sensitive data that could be exploited to harm employees, customers, and the company itself.
“In 2023, data could be used as a weapon and should be treated as such with no operational budget cuts to keep it that way,” researchers said.





Your email address will not be published. Required fields are markedmarked