
China-backed threat actors have been targeting mobile devices of Tibetans, Uyghur, and Taiwanese to harvest sensitive information. The Chinese Communist Party (CCP) has been under the radar of human rights watchdogs for targeting these ethnic groups.
A report published by Volexity, a US-based cyber security firm, states that the threat actors have been targeting mobile devices and spreading malware, which was inserted in a victim's device as a backdoor into legitimate applications.
With a high level of confidence, Volexity attributes this activity to EvilBamboo (formerly known as Evil Eye), a threat actor operating in the interest of the Chinese state.
The threat actor spreads three malware types, codenamed BADSIGNAL, BADBAZAAR, and BADSOLAR. Researchers identified that the malware is capable of collecting basic device information, such as the time zone, language, and screen resolution.
Also, it lists the user’s Ethereum accounts if they’re using the MetaMask browser extension and fingerprints the browser using a canvas-based fingerprinting technique.
Fake websites to distribute malware
In the report, researchers identified that attackers were spreading malware by creating fake websites advertising Signal, Telegram, and WhatsApp.
Researchers found that the spyware was spread through fake websites, including:
- signalplus.org
- allwhatsapp.net
- flygram.org
- groupgram.org
- ignitetibet.net
- uyghurinfo.net
- tw.tinmf.org
Some websites contain articles or surveys regarding Taiwan’s independence, however, they try to load a custom JavaScript profiling framework. Researchers believe that it can identify devices running iOS and this could have been used to selectively deliver malware.
Impersonating social media communities
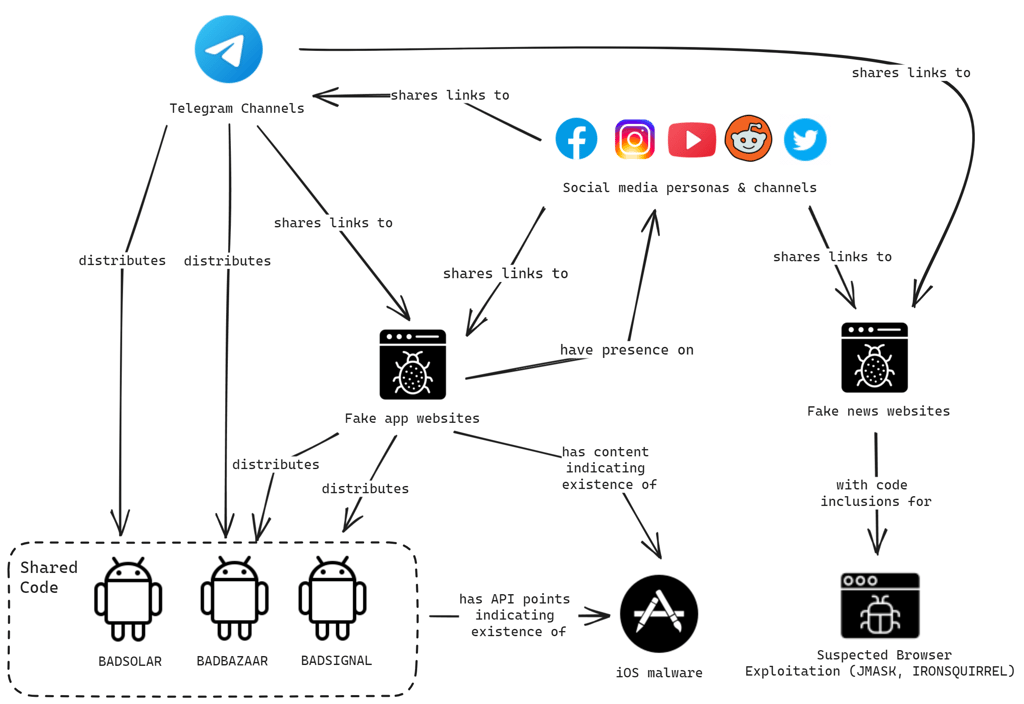
Social media is another identified means for spreading the malware. By impersonating existing popular communities on social media, the attackers have built communities on online platforms, such as Telegram, to aid in the distribution of their malware.

Researchers identified a couple of Telegram groups, like “Tibetanmaptalk” and “Tibetanphone,” promoting malicious applications. Since 2020, EvilBamboo has been targeting individuals of Tibetan ethnicity with Android spyware. To date, researchers counted more than 120 backdoored Android Package Kits (APK) that have been shared through the group.
Also, attackers used fake profiles on Facebook, Instagram, Reddit, X, and YouTube, likely to deploy browser-based exploits against targeted users.
While it may seem unusual to download apps from Telegram groups, it’s not an uncommon practice for users speaking rare languages such as Tibetan or Uyghur. These languages are not commonly supported by the official versions of apps.In one of the malicious posts, a threat actor asks for a Tibetan translation of map software named AlpineQuest, which is backdoored with BADBAZAAR and contains a link to a dedicated Telegram channel “Tibetanmaptalk.”
In addition to Android apps, one message in the group contained a link to an already deleted iOS application named “TibetOne” available in the Apple App Store.






Your email address will not be published. Required fields are markedmarked