
Network access to 7,500 organizations is being sold by a threat actor on multiple Russian hacker forums. According to the listings posted on October 3 and October 26, these mainly include educational organizations. However, the package also appears to include access to corporate networks from other verticals, such as entertainment and the bar industry.
The seller offers “convenient access” to the 7,500 compromised networks located in the USA, Canada, and Australia via Remote Desktop Protocol (RDP) and claims to be the sole cybercriminal in possession of the network access. The advert has been posted on at least two Russian hacker forums. The access is sold via an auction, with the initial bid for the entire package starting at 25 BTC (roughly $330,000) and the “Buy now” option at 75 BTC (about $1,000,000).
Protect your organization and devices against the full spectrum of cyberattacks.
Choose best antivirus softwareThose with the Bitcoin to spare would be able to exploit the thousands of vulnerable systems in a variety of ways. This includes using the powershell, managing files, editing the registry, and changing administrator rights, as well as planting malware or installing ransomware across the compromised networks.
Network access listings like these are becoming increasingly popular on hacking forums as of late, with the number of similar ads effectively tripling in September 2020 alone.
RDP: the number one intrusion vector for ransomware gangs
Remote Desktop Protocol, a proprietary protocol designed to share files across multiple devices in a network, is infamous for being rife with security holes, including the BlueKeep vulnerability (CVE-2019-0708), that make RDP exceptionally easy to exploit for threat actors.
- Make your online presence secure by using the best VPN you can get
- Use one of the top website builders to build your site in no time
- Host your website - use the best web hosting provider from the list
BlueKeep is particularly concerning because it is “wormable,” which means that it can spread automatically, without the user initiating the process. In fact, vulnerabilities like BlueKeep put Remote Desktop Protocol as the most popular intrusion vector for attackers and “the source of most ransomware incidents in 2020,” despite the fact that this critical vulnerability was found more than a year ago.
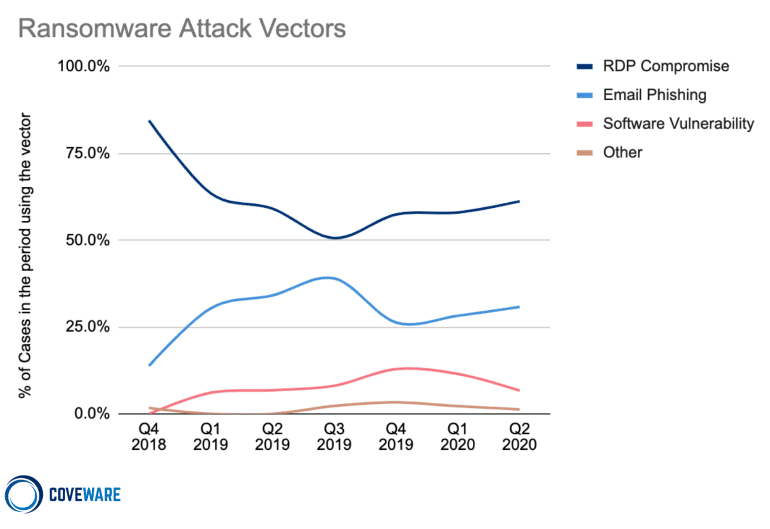
Image: Coveware
By utilizing these vulnerabilities, threat actors can carry out Remote Code Execution (RCE) attacks against the machines that use RDP. Ransomware groups exploit this protocol increasingly often, which leads to countless organizations being targeted by ransomware campaigns for immense profits.
Even the forum listing creator mentions that their access package would be a great buy for a new and aspiring ransomware gang, as carrying out an attack against 7,500 organizations would help the group make a name for itself in the cybercrime underground.
A multitude of systems still vulnerable to RDP attacks
To see how many potential targets may be currently susceptible to RDP attacks across the world, we went on the Shodan.io IoT search engine and looked for devices that had open RDP ports.
The results were quite eye-opening:

As we can see, millions of devices are still open to the public. This does not mean that all these machines are necessarily vulnerable to cyberattacks: some might be false positives, while others might be patched or otherwise protected from the common vulnerabilities associated with RDP.
However, considering how actively this attack vector is being exploited by cybercriminals in general and ransomware gangs in particular, one can safely assume that a non-trivial percentage of the open devices is vulnerable.
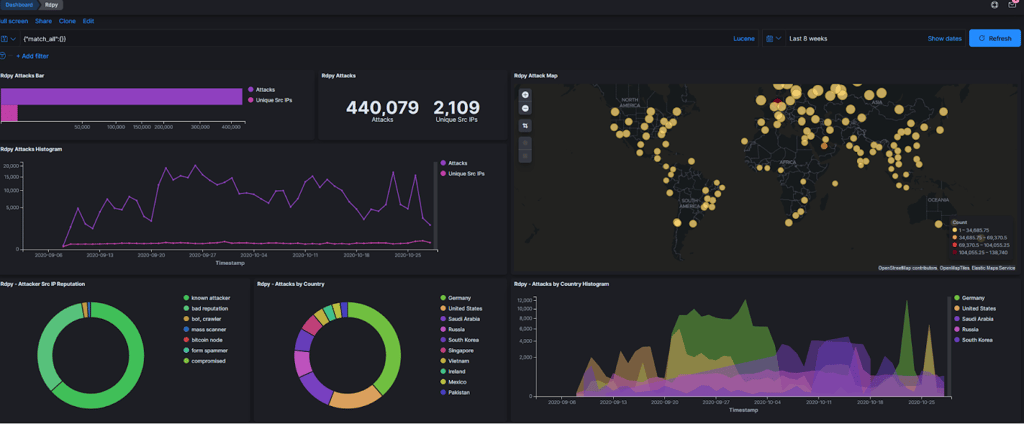
To see how often RDP vulnerabilities are being exploited by cybercriminals, let’s take a look at the data gathered from our own honeypot which tracks the number of RDP-related incidents carried out against it.
The following graph shows the staggering number of incidents or attacks suffered by the honeypot via the RDP port (440,000+) over the past seven weeks:
Now, let’s see which of our honeypot’s ports bore the brunt of these cyberattacks:
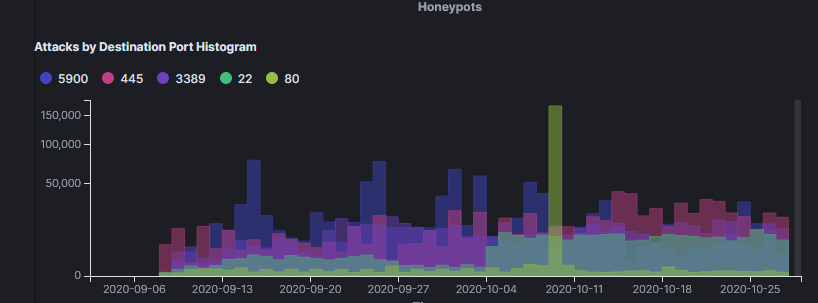
Port 3389 represents RDP, which puts it among the top 3 most-attacked ports during the seven-week period. Ports 5900 (VNC) and 445 (SMB) are popular intrusion vectors as well, often used by threat actors to gain initial access to corporate networks.
The cost of clicking “Remind me tomorrow” for 18 months in a row
Between the sharp rise in attacks targeting RDPs, the surprising growth of the ransomware “industry,” and the overall surge of cybercrime over the past several years, organizations now have a rapidly dwindling supply of excuses for getting their networks compromised due to ancient vulnerabilities, which is the direct result of not keeping their systems up to date.
So, what should organizations do to avoid seeing access to their networks being sold on a Russian hacker forum? Let’s see:
- Patch the vulnerability.
- See if they don’t have machines with exposed RDP ports that are unpatched.
- Keep their networks and devices protected with a strong firewall and a quality antivirus.
Finding these kinds of listings on hacker forums and seeing millions of potential sitting-duck systems on IoT search engines is particularly frustrating because the solution to the RDP problem is so simple. One can only hope that the day when organizations (especially those in the educational sector) start taking security updates seriously, arrives sooner rather than later.






Your email address will not be published. Required fields are markedmarked