
Popular mobile role-playing game (RPG) Tap Busters: Bounty Hunters spilled sensitive user data.
The research by Cybernews has discovered that the Tap Busters: Bounty Hunters app had left their database open to the public, allegedly exposing users’ private conversations for at least five months.
Also, app developers had sensitive data hardcoded into the client side of the app, making it vulnerable to further data leaks.
Tap Busters: Bounty Hunters is an idle RPG game with more than one million downloads on Google Play Store and a 4.5-star rating based on more than 45,000 reviews. In the game, players take on the role of bounty hunters trying to become masters of the galaxy. They defeat villains and collect loot as they travel through different alien realms. Idle game mechanics mean that players can progress in-game without constant input.
Significance
Researchers discovered that Tap Busters: Bounty Hunters leaked data through unprotected access to Firebase, Google's mobile application development platform that provides cloud-hosted database services. Anyone could have accessed the database in the meantime.
The 349MB-strong unprotected dataset contained user ids, usernames, timestamps, and private messages. If the data leaked had not been backed up and a malicious actor had chosen to delete it, it is possible that the user's private messages would have been permanently lost without the possibility of recovery.
Along with an open Firebase instance, the developers left some sensitive information, commonly known as secrets, hardcoded in the application's client side. The keys found were: fir ebase_database_url, gcm_defaultSenderId, default_web_client_id, google_api_key, google_app_id, google_crash_reporting_api_key, google_storage_bucket.
Hardcoding sensitive data into the client side of an Android app is unsafe, as in most cases, it can be easily accessed through reverse engineering.
No response
The game's developer is Tilting Point, which owns several other successful games with a large player community. Some of these games have over five million downloads. The app developer was informed of the data spill but failed to close public access to the database.
The app developers did not reply to Cybernews questions about the duration of the instance's public accessibility or the possibility that malicious actors might exploit hardcoded secrets, resulting in sensitive data breaches.
However, at the time of writing, the app’s firebase instance had so much data that acquiring it all in one run became impossible for threat actors due to Google’s data transferring policies, in effect rendering the instance as having a too large payload to be acted upon.
Leaky Android Apps
Tap Busters: Bounty Hunters is one of the thousands of apps on the Google Play Store vulnerable to data leaks.
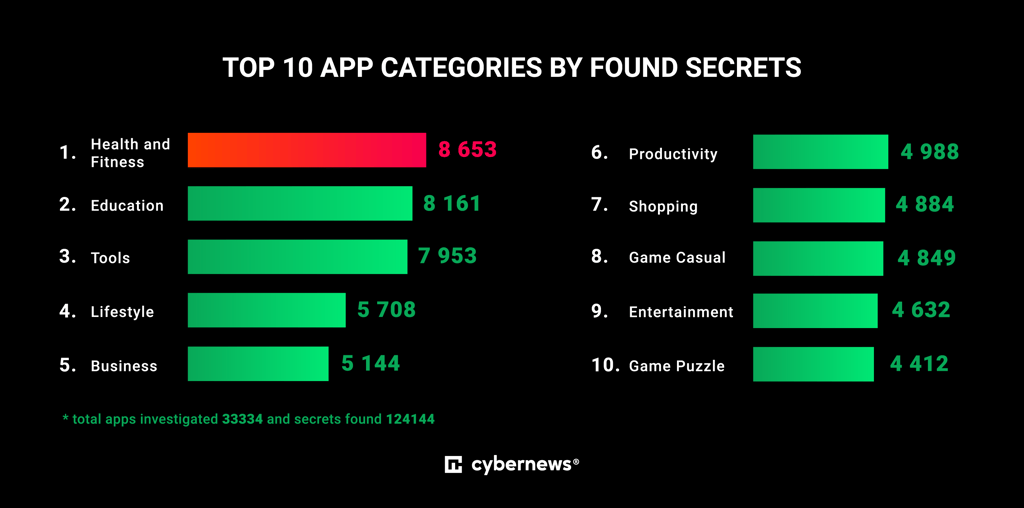
Earlier this year, Cybernews analyzed over 33,000 Android apps and found that the most sensitive types of hardcoded secrets left exposed were application programming interface (API) keys used to authorize projects, links to open Firebase datasets, and Google Storage buckets.
Results showed that over 14,000 apps had Firebase URLs on their front end. Out of these, 600 were links to open Firebase instances. This means that by examining the public information of an app, a malicious actor could gain access to its open database and potentially access user data.
The five categories of apps that contained the most hardcoded secrets were health and fitness, education, tools, lifestyle, and business.






Your email address will not be published. Required fields are markedmarked