
Once a niche technology, drones are about to explode in terms of market growth and enterprise adoption. Naturally, threat actors follow the trend and exploit the technology for surveillance, payload delivery, kinetic operations, and even diversion.
There exists a class of tiny and highly maneuverable devices that introduce a variety of cybersecurity risks you probably haven’t considered before.
Drones currently occupy a unique legal position as they are classified as both aircraft and networked computing devices. From a malicious drone operator perspective, this inherently grants a high level of advantageous legal ambiguity and protection to criminals operating drones as counter-attacking efforts taken by victims may violate protective regulations or laws applicable to aircraft, but also anti-hacking laws meant to provide protections to personal computers, their data, and networks.
This article is going to explore cybersecurity considerations surrounding drone platforms through an initial review of drone market trends, popular drone hacking tools, and general drone hacking techniques that may be used to compromise enterprise drone platforms, including how drone platforms themselves may be used as malicious hacking platforms.
A secondary outcome of this article is to help spur awareness around a once niche space of technology that is about to explode in terms of market growth and enterprise adoption.
Market overview
According to research firm Statista, the global retail drone market is expected to reach $90 billion by 2030, with Defense, Enterprise, and Logistics being the primary industries driving growth. Within the United States alone, nearly 300,000 commercial pilot licenses have been issued as of 2022, compared to nearly 1 million individual drones that have been registered with the Federal Aviation Authority(FAA) per weight and commercial compliance rules2.
This number does not account for drone platforms operated by amateur pilots or hobbyists that do not require professional licensure or those that operate under weight limitation thresholds (typically <250 grams = no licensing/registration requirement.) that require registration with local or federal authorities.
In China, the retail drone market reached $15 billion in 2021, with projections to exceed $22 billion by 2024. Drone pilot licenses issued throughout China exceed the United States, with over 780,000 registered pilots and close to 850,000 registered drones.
These numbers inform of the possibility that a once uncluttered skyline may soon be teeming with millions of drone aircraft, and questions begin to arise regarding the sanctity of enterprise security, privacy, and potential cybersecurity threats sourcing from the sky.
Departing from the general market statistics concerning drones, it is prudent to better understand how a flying laptop poses a threat to enterprise operations. From a cybercriminal perspective, drones are an ideal tool to carry out malicious attacks because they generally provide a greater layer of separation between the bad actor, the aircraft itself, and the actions executed by the physical drone platform.
Laptops or workstations primarily operate in 2D space physically and are more easily associated to an end user whereas a flying, computerized aircraft with a range of 10km can be harder to trace to a specific individual or geographical area. Drones also offer cybercriminals a great degree of flexibility in their usage because they are affordable, highly modifiable, they can operate across a greater range of weather conditions, flight distances, and altitudes versus semi-stationary workstations hackers traditionally operate from.
Aerial trespass
Let’s dive into some examples of how enterprises must account for external drones entering their airspace and cyber threats to drones operated by the enterprise.
An external drone not owned or operated by the enterprise can achieve many objectives useful to cyber criminals wishing to attack an organization. These objectives include but are not limited to site surveillance, photographic reconnaissance, physical or electronic payload delivery, kinetic operations (flying a drone into something for a specific purpose), and as a diversionary tactic.
A prime example is using a drone to fly over a potential target to visually map out physical security barriers prior to a robbery, identifying security guard patrol locations and schedules, or determining if anyone even responds to the aircraft while it is present. Drone platforms are also commonly used globally to smuggle contraband such as drugs, cellphones, or weapons into prisons with an alarming success rate.
Enterprises with sound counter drone programs in place may still be limited in how they respond to external drone threats as it is commonly unlawful to simply shoot them down or capture them. Within the United States for example, operating a drone within Class G, uncontrolled airspace over another entity's property without advanced notice is legally allowed. Some state and local laws allow property owners and businesses to file trespass claims against operators but the difficulty is often associating the drone platform to its operator and serving them written notice.
Similar laws allowing some degree of aerial trespass exist throughout other international jurisdictions including Australia, Singapore and the United Kingdom with certain limitations. Enterprises are at a further disadvantage as malicious drone platforms cost anywhere from a few hundred to a thousand dollars while Counter Unmanned Aircraft Systems (CUAS) can cost well into the millions of dollars per annum simply just for the software subscription, not the personnel to operate it.
From a risk management perspective, drone mitigation using detective controls such as CUAS are simply non-sustainable for many enterprises as the costs will typically far exceed the inherent risks.

Attacks against enterprise-owned drones
Cyberattacks against drones that an enterprise owns and operates is an entirely different animal. Further considerations must be taken to secure onboard storage of the drone, ensure routes drones travel are relatively safe (i.e., free from obstacles, sparsely populated, etc.) and that Wi-Fi or Radio Frequency (RF) signals used by drone platforms are properly encrypted against eavesdropping or manipulation.
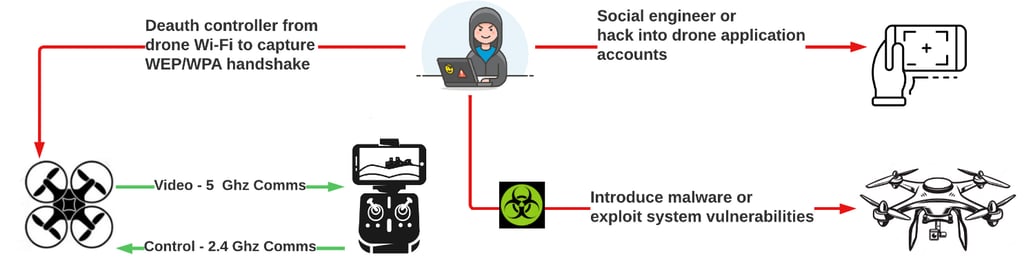
Most drone platforms provide an onboard mini or micro storage disk port for local storage. Common attacks against enterprise drones include platform takeover, where an attacker uses RF, Wi-Fi or a subscription service like Aerial Armor to detect flight paths of a drone in a geographical area, perform de-authentication attacks, take over control of the drone and land the stolen drone in a location of its choosing.
From here, the attacker can physically remove onboard storage and pilfer the contents, depending on the storage configuration or potentially introduce malware via the SD card port, then leave the drone for the owner to find. Cybercriminals may also attempt to poison the geolocation instructions or Return To Home (RTH) coordinates of the drone to intentionally damage the aircraft or use it for other nefarious purposes causing the enterprise monetary damages in lost drone equipment, legal trouble, and reputational harm.
Let’s overview common tools or platforms built specifically to hack drones and see how some of these may assist cybersecurity applications in real world scenarios.
Dronesploit
The first tool previewed in this article is Dronesploit, a Command Line Interface (CLI) solution which directly resembles and is similarly structured to the Metasploit Framework. Dronesploit seeks to combine various tools useful for penetration testing specific to drone platforms.
Dronesploit is dependent on Aircrack-ng being installed and fully functional in addition to having an appropriate wireless network adapter capable of sniffing wireless networks and performing packet injection. The first step before launching Dronesploit is to put an available wireless network interface into monitor mode using the “Airmon-ng start wlan0” command. Monitor mode status can be verified before proceeding by issuing the “iwconfig” command.

Once the wireless network interface is placed into Monitor mode, Dronesploit should be launched from a secondary command window while allowing the monitored interface to remain active. Dronesploit is ready to use once all warning messages stop prompting the user to take specific action (such as starting an interface in ‘Monitor’ mode).
Dronesploit is ideal for assessing Wi-fi based drones like DJI Tello or Hobbico drone platforms but has some general-purpose auxiliary modules that are effective across many drone models.

Some of broadly useful commands reside in Dronesploit’ auxiliary family of modules. Metasploit users will be happy to see that Dronesploit leverages familiar command-lets to select modules, set various options and execute drone attacks.
Below is an example of the “wifi/find_ssids” command, outlining the monitored interface being used, and time out values. Dronesploit can also directly call various elements of aircrack-ng to capture and attempt to crack WPA2 wireless handshakes making it a highly versatile tool.

Danger Drone platform
The next tool the article will preview is the Danger Drone platform, as developed and discussed by penetration testing provider Bishop Fox. Dangerdrone is an affordable, mobile drone platform, leveraging a 3D printed airframe, with a Raspberry Pi small single-board computer.
It is optimized to carry a Wi-Fi pineapple for wireless network auditing and several other USB peripherals like Alfa wireless network interfaces to support aerial penetration testing efforts from a flying drone. Imagine a drone flying onto private property unnoticed, landing on the roof of a building, and performing wireless network attacks against the computers underneath or around it. Scary stuff…
The article will conclude with some more pointed drone pentesting examples using Aircrack-ng itself. Using the monitored interface from the Dronesploit example, aspects of Aircrack-ng can be used to perform several useful drone security tests, including identification of wireless drone networks, de-authentication of connected devices like a drone controller, or cracking of the WEP/WPA keys.
The below example shows how the “Airodump-ng wlan0” command is useful for identifying nearby drone wi-fi signals, including the MAC address of the broadcasting device, the network encryption scheme, and the wireless authentication standard used by the drone. In the example below, a hobbyist-level drone from Sanrock using Open Wi-Fi and a DJI drone with enhanced Wi-Fi security protections are identified.

Drones will establish a private Wi-Fi network to allow user interaction between the controller and mobile application for drone operations. The Sanrock drone has an open Wi-fi network standard that doesn’t require authentication, such as use of a Pre-shared key, to connect to it. A quick way to find the IP address of the drone Wi-Fi network in question is to try connecting to the broadcasting SSID from either Kali Linux or another system, like a mobile phone and once connected, running “ipconfig /all” to compare the IP address information to the connection properties of the drone network. Vulnerability scans and various other tools can be directed at this address to uncover other targets and start assessing them for points of entry.

Switching back to Aircrack-ng, a de-authentication attack can be accomplished using airodump-ng in conjunction with aireplay-ng. These attacks are useful for either drone takeover or obtaining the wireless network key for offline cracking. Attackers can successfully sabotage Return to Home (RTH) instructions using geolocation poisoning, where the communications between pilots and the drone platform are interrupted, initiating internal drone safety routines that automatically instruct the drone to navigate to and land in a pre-configured location, allowing physical theft of the platform.
The below command highlights how Airodump-ng is used to first discover a connected station (or client like a mobile device), and send de-authentication frames that disconnect the client. In this case, the Sanrock drone has no Wi-fi authentication mechanism like a WPA pre-shared key to capture, but tests did result in mobile application disconnection and drone takeover.

The second command “airodump-ng -c 1 –bssid 98:C9:7C: -w capture19 wlan0” is used to start a live capture file which is used primarily to capture WEP/WPA pre-shared keys and other useful details. The capture file can be sent to aircrack-ng later to attempt brute force cracking of the pre-shared key but is outside the scope of this article. With the capture running, the “aireplay-ng -0 100 -a 98:C9:7C13:8B:34 -c 3C:2E:FF:BE:9F:03 wlan0” command can be issued which results in de-authentication of the connected client. Notice a high degree of lost ethernet frames, indicating an interrupted connection. Assessments could continue using tools like Nmap and its scripting engine to locate open ports or OpenVAS to perform vulnerability scanning. With this in mind, a common trend begins to emerge showing how similar drone platforms are to mobile computing devices like laptops, and enterprises should consider assessing drone risk in a similar context.

Disclaimer
This article doesn’t encourage unauthorized assessment of drone platforms not owned by the reader, nor does it educate the reader on in-depth hacking techniques against such platforms. The article simply demonstrates very basic approaches that may be used to assess enterprise drone security and assist enterprises in formulating defensive strategies based on their risk profile.
The article briefly showcased short-term drone market projections, which reflect the likelihood of drone presence globally. The article covered common malicious use cases enacted by bad actors, such as reconnaissance, some of the tools and platforms available to cybercriminals, and live examples of how these tools may be used maliciously.
Enterprises are accustomed to contending with cyber threats, which operate on the same ground-based playing field as they do. Now, they must be more vigilant than ever, as they must account for cyberattacks sourcing from the sky. It is vital that enterprises understand their position on drone-based risks and ensure appropriate policies, procedures, and that personnel are positioned to respond to these threats accordingly.






Your email address will not be published. Required fields are markedmarked