
The City of London Police have arrested seven teenagers in relation to the Lapsus$ extortion group, the BBC said.
"Seven people between the ages of 16 and 21 have been arrested in connection with an investigation into a hacking group. They have all been released under investigation. Our inquiries remain ongoing," the City of London Police said.
A 16-year-old from Oxford, who lives with his mom, has been accused of being one of the leaders of the Lapsus$ gang, which recently has made headlines by publicly going after the big tech companies.
Before announcing the Okta breach, Lapsus$ had threatened to breach Microsoft. The same day that it released screenshots supporting the Okta hack claim, Lapsus$ also dropped what it claims to be an incomplete Bing (45%), Bing Maps (90%), and Microsoft virtual assistant Cortana (45%) source code.
Lapsus$ has also claimed responsibility for the cyberattack on Nvidia and Samsung.
Microsoft noted that, unlike most activity groups that stay under the radar, Lapsus$ doesn’t seem to cover its tracks.
Microsoft said that Lapsus$ deploys several tactics that other threat actors use less frequently.
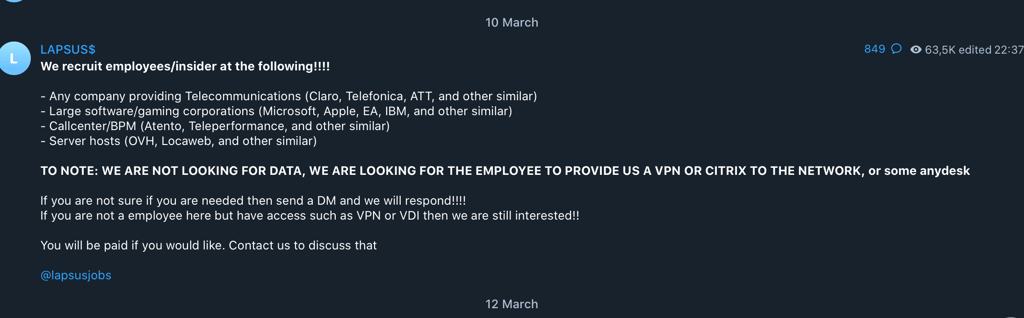
“Their tactics include phone-based social engineering; SIM-swapping to facilitate account takeover; accessing personal email accounts of employees at target organizations; paying employees, suppliers, or business partners of target organizations for access to credentials and multifactor authentication (MFA) approval; and intruding in the ongoing crisis-communication calls of their targets,” Microsoft said in its latest blog post.
Lapsus$ focuses on compromising user identities to gain initial access to an organization. Compromised credentials allow the threat actor to access internet-facing systems and applications, such as virtual private network (VPN), remote desktop protocol (RDP), virtual desktop infrastructure (VDI), or Identity providers (including Azure Active Directory, Okta).
Compromised Microsoft account
As mentioned above, Lapsus$ said it had exfiltrated a portion of Microsoft source code. The company has acknowledged that there was a compromise.
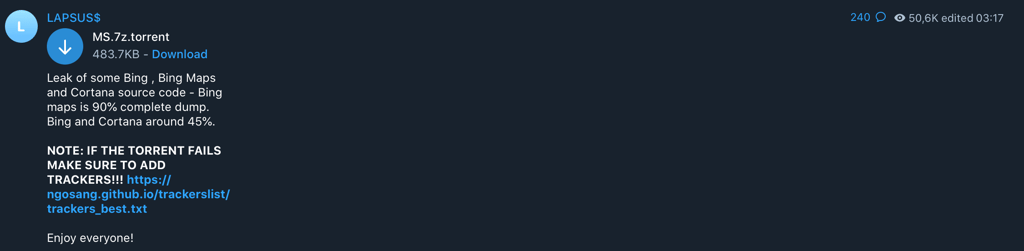
“Our investigation has found a single account had been compromised, granting limited access. Our cybersecurity response teams quickly engaged to remediate the compromised account and prevent further activity,” it said.
Microsoft highlights that it does not rely on code secrecy as a security measure, and viewing source code does not lead to elevation of risk.
“The tactics DEV-0537 used in this intrusion reflect the tactics and techniques discussed in this blog. Our team was already investigating the compromised account based on threat intelligence when the actor publicly disclosed their intrusion. This public disclosure escalated our action allowing our team to intervene and interrupt the actor mid-operation, limiting broader impact.”
Lapsus$ has exaggerated the scale of the access to Okta
Authentication firm Okta has reached out to all 366 customers potentially affected by the recent breach. Lapsus$ extortion group had access to the support engineer’s computer for five days in January.
On March 22, Lapsus$ shared a number of screenshots that seemed to be of Okta’s internal system. According to Okta, screenshots were taken from a computer used by Okta third-party customer Sitel’s support engineers. Sitel is an Okta sub-processor that provides Okta with contract workers for our Customer Support organization.
“The sharing of these screenshots is embarrassing for myself and the whole Okta team,” Okta Chief Security Officer David Bradbury said.
Lapsus$ had access to the engineer’s computer for a period of five days between 16-21 January 2022. It has determined that the maximum potential impact is 366 (approximately 2.5% of) customers whose Okta tenant was accessed by Sitel.
Meanwhile, Lapsus$ has suggested that they had maintained access for two months following 21 Jan 2022.






Your email address will not be published. Required fields are markedmarked