
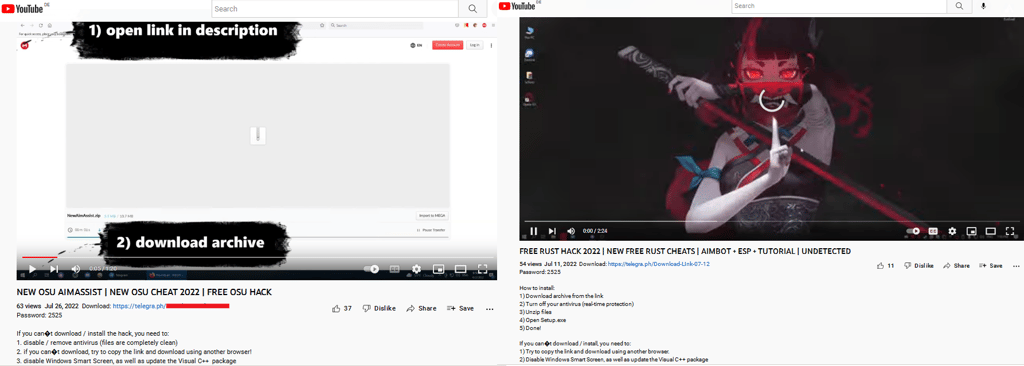
Stealer malware disguising itself as a YouTube channel offering cheats and hacks for popular video games has been spotted by cybersecurity watchdog SecureList.
The stealerware that delivers the payload – which harvests victim gamers’ online credentials – is known as RedLine and has been on SecureList’s radar since 2020.
“RedLine is currently one of the most common Trojans used to steal passwords and credentials from browsers, FTP clients and desktop messengers,” said SecureList. “It is openly available on underground hacker forums for just a few hundred dollars, a relatively small price tag for malware.”
The YouTube cheat channel was taken down by the platform’s owner Google for violating its community guidelines after it was detected, the tech giant said. Before this was done, gamers could access cheats and hacks for popular games including Farming Simulator, Farthest Frontier, FIFA 22, Final Fantasy XIV, LEGO Star Wars, and Spider-Man.
But the lure aimed to turn the tables on dishonest gamers, by drawing them in to be hit by RedLine’s payload, which then siphoned off their vital information, including “usernames, passwords, cookies, bank card details, autofill data from Chromium- and Gecko-based browsers, data from cryptowallets, instant messengers and FTP/SSH/VPN clients, as well as files with particular extensions from devices.”
Cheating the cheaters
“Stealer-type malware is often distributed under the guise of game hacks, cheats and cracks,” SecureList added. “Cybercriminals lure victims with ads, as well as instructions on how to hack games. At the same time, the self-propagation functionality is implemented using relatively unsophisticated software, such as a customized open-source stealer.”
RedLine’s capacity to multiply and spread itself is complemented by its ability to download and run third-party programs, remotely execute commands, and open links in a default browser.
“The stealer spreads in various ways, including through malicious spam emails and third-party loaders,” said SecureList. “All this is further proof, if any were needed, that illegal software should be treated with extreme caution.”






Your email address will not be published. Required fields are markedmarked