
Hacker using pseudonym Rektengle claims to have hacked into Rogers days before the outage to help them secure the perimeter.
The company neither confirmed nor denied the incident but strongly emphasized that a maintenance update caused their outage.
Unprecedented outage
On July 8, Rogers, a Canadian telecoms operator with approximately 10 million wireless subscribers, experienced an outage that "caused real pain and significant frustration to everyone."
"Canadians were not able to reach their families. Businesses were unable to complete transactions. And critically, emergency and essential calls could not be completed," President and CEO of Rogers Communications Tony Staffieri said.
The glitch lasted for 19 hours. The Canadian Radio-television and Telecommunications Commission (CRTC) has required a detailed account from Rogers as to "why" and "how" this happened, saying, "Events of this magnitude paralyzing portions of our country's economy and jeopardizing the safety of Canadians are simply unacceptable."
According to Reuters, the Canadian minister for industries, François-Philippe Champagne, announced a probe over the network outage.
According to Staffieri, a maintenance update in their core network caused a network failure.
However, one hacker who wanted to be referred to by his Twitter handle, Rektengle, said he tried to warn the company days before the outage by reporting and exploiting the bug he allegedly found in their systems.
The alleged hack
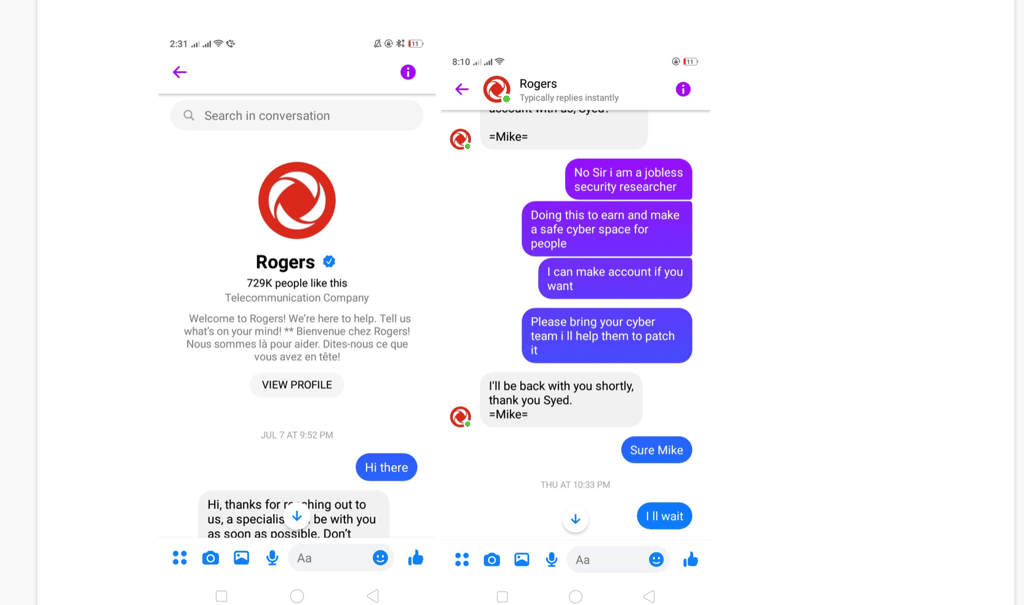
Rektengle, who says to be hunting for bugs for 17 years, claims to have reported the bug on July 7 – a day before the outage – by a Facebook message.
But before reporting the vulnerability, he exploited it. Rektengle claims to have hacked into Rogers to test the susceptibility but allegedly did no harm. Rektengle told Rogers that he was able to access their active directory and internal data. From the screenshots provided to Cybernews as proof, we can neither confirm nor deny this was the case.
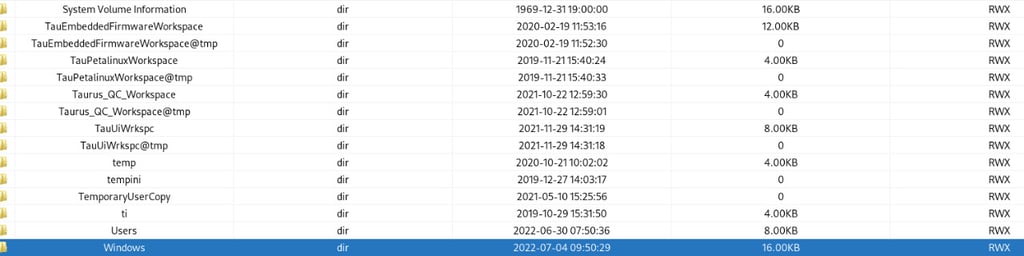
Hacker said the bug was related to Log4j and described to us the way he allegedly managed to hack into Rogers. However, he asked not to disclose his method to the public.
From the screenshots, it seems that Rektengle was in touch with Rogers support for days, claiming he wanted to help the company patch the vulnerability. In one message, an anonymous Rogers support manager says the company was hacked.
“I know we were hacked however there’s further investigation being done. We will be giving a credit for the day you had no service,” [sic] the message reads.

Rogers’s statement
Cybernews repeatedly contacted Rogers to learn more about the alleged cyber incident.
"With regards to your question, I can confirm that the recent outage was not a result of a cyber security incident. We've narrowed down the cause to a network system failure following a maintenance update to our core network, which caused a router malfunction early Friday morning," the company's spokesperson told us via email.
He declined to comment more on Rektengle's claims. When repeatedly asked to verify whether the support manager's message was authentic, the spokesperson sent us this statement instead:
"Please refer to my previous response with regards to your question." He also shared a message from Staffieri.
"I also want to share what we know about what happened yesterday. We now believe we've narrowed the cause to a network system failure following a maintenance update in our core network, which caused some of our routers to malfunction early Friday morning. We disconnected the specific equipment and redirected traffic, which allowed our network and services to come back online over time as we managed traffic volumes returning to normal levels."
Not the right way to hunt bounties
Rektengle repeatedly told me he is hunting for bugs to make the world safer. “Please bring your cyber team i ll help them to patch it,” [sic] one of his messages to Rogers reads.
However, even with the best intentions, testing a bug by hacking into a company is not the right thing to do. Rektengle claims Rogers owes him a bug bounty for pointing out the vulnerability. Still, in reality, the hacker’s actions could be equated to extortion and prompt a specific entity to press charges.
“This is an interesting story from two points of view. It is common for businesses to brush off found vulnerabilities and issue statements of doing maintenance. However, the severity of this maintenance raises eyebrows, senior Cybernews researcher Mantas Sasnauskas said. “On the other hand, the person that tried to report it shouldn’t have made threats, and his or her Twitter profile doesn’t seem like a normal case of bug bounty hunting. There are policies and laws, not to mention ethics, that one must follow, and one should definitely not report vulnerabilities on social media making threats.”
The sentiment towards white hat hackers has been shifting for quite some time. Recently, the Department of Justice said good-faith security researchers who probe or hack systems to point out vulnerabilities and help organizations patch them would no longer face charges.
However, even good-faith hackers must follow specific protocols, for example, submit bugs through bug bounty platforms or programs instead of reporting them to the corporate social media accounts, leave alone hacking into the company to prove the bug is exploitable.






Your email address will not be published. Required fields are markedmarked