
The top 10 ransomware attacks observed since 2020 have earned threat actors nearly $70 billion in Bitcoin. Why are cybercriminals relying on this particular cryptocurrency so much?
“Moving into 2023, ransomware remains a major threat to organizations. Just earlier this month, The Guardian and the Royal Mail revealed to have been hit by severe ransomware attacks,” a new report by Immunefi, a bug bounty and security platform for Web3, reads.
The company’s researchers detailed the top 10 ransomware attacks since 2020 and concluded that Bitcoin had been the most popular cryptocurrency among the gangs during those years.
While cybercriminals have a wide range of options for ransom payments, including USDC, Ethereum, or even Monero, they still rely on Bitcoin.
“This choice is likely because Bitcoin is the most well-known and easily accessible cryptocurrency for targeted users and organizations,” the report reads.
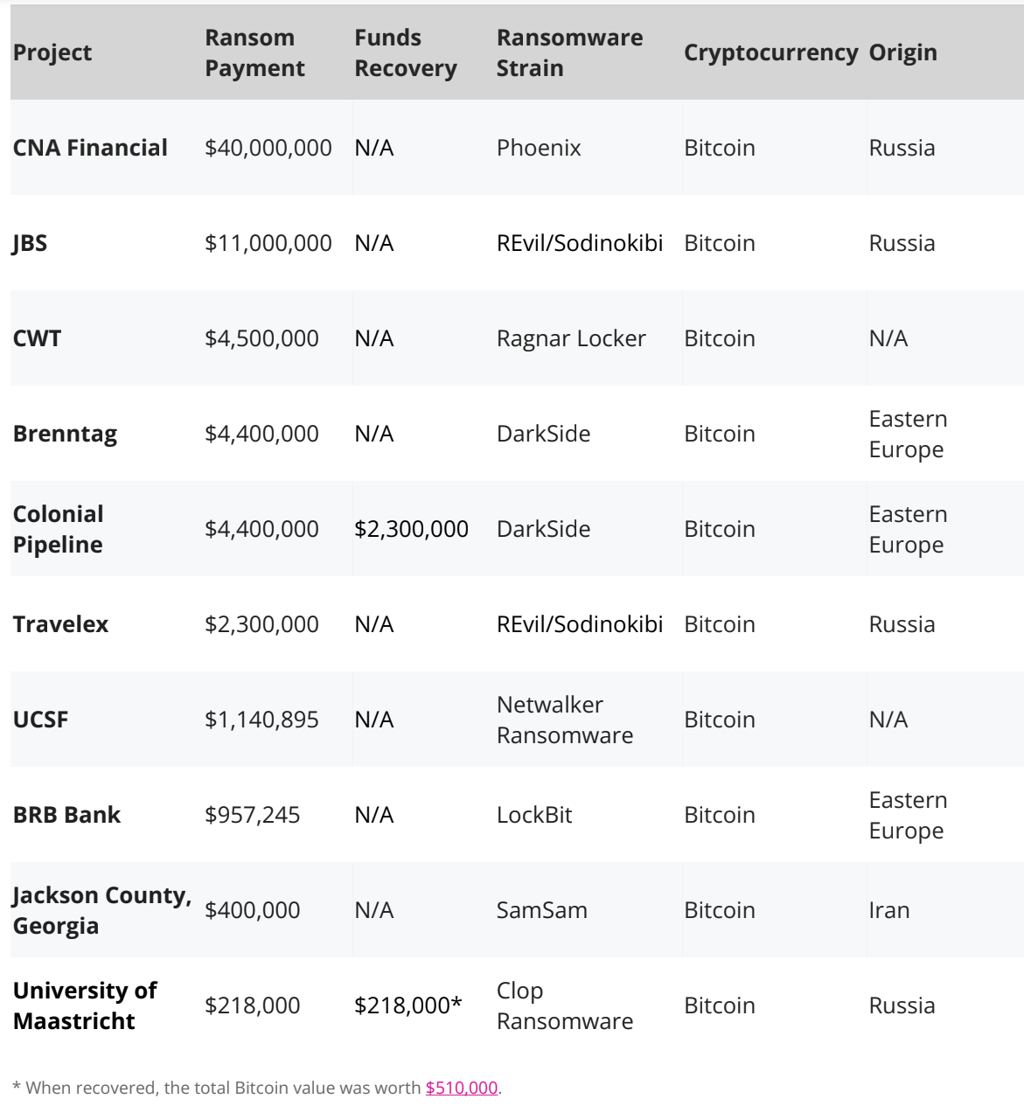
While analyzing the top 10 attacks, researchers detected eight specific ransomware strains, with REvil/Sodinokibi and DarkSide being key actors based on the total number of attacks and Phoenix group being responsible for the highest profiting attack.
And while criminals enjoy cryptocurrency due to its apparent anonymity, their transactions are somewhat traceable.
Finding criminals is still manageable because, on the Bitcoin network, it’s possible to view all addresses that the ransomware recipient address has ever interacted with and potentially trace that chain to the real owner. Everyone leaves a digital trace online,” Immunefi said.
Experts are able to find patterns and connections between the cluster of illicit actors and clusters of services, exchanges, other illicit actors, and personal wallets.
“In total, $2,518,000 has been recovered from ransom payments in two specific situations. This number makes up 3.6% of the top crypto ransomware payments. Colonial Pipeline recovered $2,300,000 from its initial $4,400,000 ransom payment, and the University of Maastricht recovered the full $218,000 ransom payment,” the company explained.






Your email address will not be published. Required fields are markedmarked