Retail giant Vevor leaked user location and payment data for almost five months

An online retailer specializing in tools and equipment for DIYers and professionals left a database with sensitive user information, including payment details, open to the public.
Vevor is a retail giant with 40+ warehouses in the US, Canada, the UK, Australia, and Germany, among other countries. It ships over one million products to professionals and DIYers worldwide, claiming it “has satisfied” over 10 million customers in over 200 countries.
Recently, the Cybernews research team was informed that Vevor left a multi-terabyte database exposed. Upon close inspection of the instance, we discovered that the company was leaking sensitive user data: full names, physical addresses, email addresses, phone numbers, order details, partial payment details, payment logs, and other tracking information.
Our investigation revealed that the database was first exposed on July 12, 2022, and leaked sensitive information for nearly five months. Vevor removed the database from public access in the first week of December after being repeatedly contacted by the Cybernews research team with the request to protect user data as soon as possible.

Cybernews has reached out to the company to learn more about the breach but received no response prior to publication. The database is now closed, and user data remains safe. That is, of course, under the condition that threat actors haven’t already retrieved the disclosed information.
“The leak could have financially damaging consequences. The data leaked is enough to create targeted phishing/vishing campaigns from your shipping courier, as all the information is available to the threat actor. If more leaks containing specific customer data exist, it is just another piece of the puzzle until all the private information is leaked and allows for online identity theft, causing financial damages, irreversible credit scores, and hours or days, or months wasted trying to get it fixed,” Cybernews research team said.
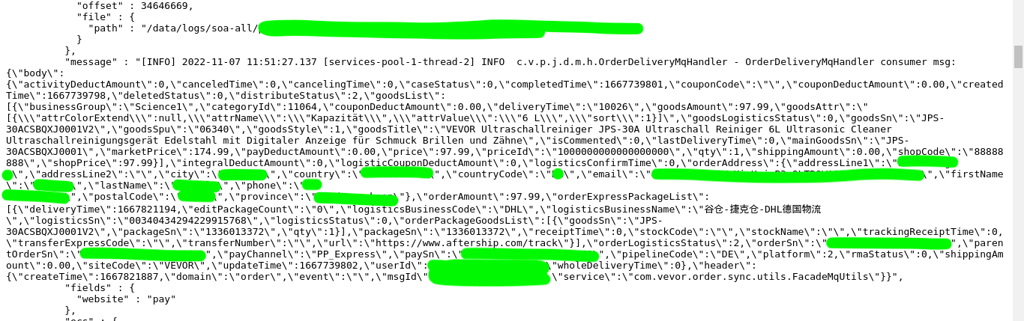
After reviewing the data samples, our researchers noticed that every Paypal authorization and capture process is logged into the same database. Paypal creates encrypted tokens for their transactions, which include payment tokens, payer IDs, transaction IDs (post payment), and so on.
“Changing values before payment is captured could reroute money flow to different PayPal accounts but still be marked as a successful transaction for the Vevor order system, causing a double loss for the company as it would be giving equipment away for free,” researchers warned.
Cybernews investigation points to the fact that Vevor has experienced a misconfiguration error on different servers at least 30 times, exposing sensitive information to the public.






Comments
Your email address will not be published. Required fields are markedmarked