8 most popular password cracking techniques: learn how to protect your privacy
Being behind major reports like The Mother of All Breaches and WhatsApp Data Leak, our in-house cybersecurity experts conduct independent, unbiased testing and thorough analysis of password managers, helping users confidently manage their credentials and sensitive information.
We prioritize transparency by openly sharing detailed descriptions of our in-house testing procedures and methodologies.
Learn more
There are many ways to hack into an account. Password cracking is one of them – it involves using various computational and other methods to break through the password authentication step. Nowadays, you can even find specialized password cracking tools, which don’t have to be used only for ill purposes.
To avoid becoming a victim of password cracking, you can also make use of password management and generator tools. They encrypt your passwords with unbreakable ciphers and help create virtually uncrackable passwords at a wallet-friendly price.

In this article, I discuss 8 password cracking techniques. Keep on reading to find out what password cracking is and how it’s done.
What is password cracking?
Password cracking means recovering passwords from a computer or from data that a computer transmits. This doesn’t have to be a sophisticated method. A brute-force attack where all possible combinations are checked is also password cracking.
If the password is stored as plaintext, hacking the database gives the attacker all account information. However, these days most passwords are stored using a key derivation function (KDF). This takes a password and runs it through a one-way encryption cipher, creating what’s known as a hash. The server stores the hash version of the password.
It’s easy to try different hashed passwords at a high rate when using a GPU or botnet. That’s why most password hash functions use key stretching algorithms, which increase the resources (and, therefore, time) needed for a brute-force attack.
Some methods of password cracking become significantly more difficult if your password uses salting or key stretching. Unfortunately, there are still some services that store unencrypted or weakly encrypted passwords on their servers.
How to create a strong password

Top 8 password cracking techniques used by hackers
Naturally, cybercriminals want to use the easiest method available for password cracking. More often than not, that method is phishing, described in detail below. As long as the human is the weakest link of any security system, targeting them is the best bet. If that fails, there are plenty of other password cracking techniques to try.
While passwords are a very popular account security tool, they aren’t necessarily the safest option. That’s especially the case if a user creates a weak password, reuses it, and stores its plaintext copy somewhere online. That’s why using a password manager, biometric data (which has its cons too) or adding a second factor will make most of the cracking methods below useless.
A typical password cracking attack looks like this:
- Get the password hashes
- Prepare the hashes for a selected cracking tool
- Choose a cracking methodology
- Run the cracking tool
- Evaluate the results
- If needed, tweak the attack
- Go to step 2
Now let’s discuss the most popular password cracking techniques. There are many cases when these are combined together for greater effect.
1. Phishing
_1.jpg)
Phishing is the most popular technique that involves luring the user into clicking on an email attachment or a link that contains malware. The methods for doing so usually involve sending some important and official-looking email that warns to take action before it’s too late. In the end, password-extracting software is installed automatically or the user enters his account details into a look-alike website.
There are different types of phishing tailored for a particular situation, let's look at the few common ones:
- Spear phishing targets a particular individual and tries to gather as much personal information as possible before the attack.
- Whaling targets senior executives and uses company-specific content, which can be a customer complaint or a letter from a shareholder.
- Voice phishing involves a fake message from a bank or some other institution, asking a user to call the helpline and enter his account data.
2. Malware
As you’ve seen, malware is often part of the phishing technique too. However, it can work without the social engineering factor if the user is naive enough (they usually are). Two of the most common malware types for stealing passwords are keyloggers and infostealers. As their names imply, the former sends all your keystrokes to the malicious hacker, and the latter uploads the screenshots.
Other types of malware can also be used for password stealing. A backdoor trojan can grant full access to the user’s computer, and this can happen even when installing so-called grayware. Also known as potentially unwanted applications, these programs usually install themselves after clicking the wrong download button on some website. While most will display ads or sell your web usage data, some might install much more dangerous software.
3. Social engineering
This password cracking technique relies on gullibility and may or may not employ sophisticated software or hardware – phishing is a type of social engineering scheme.
Technology has revolutionized social engineering. In 2019, cybercriminals used AI and voice technology to impersonate a business owner and fooled the CEO into transfering $243,000. This attack demonstrated that faking voice is no longer the future, and video imitation is already becoming commonplace.
Usually, the attacker contacts the victim disguised as a representative of some institution, trying to get as much personal info as possible. There’s also a chance that by posing as a bank or Google agent, he or she might get the password or credit card info right away. Contrary to the other techniques, social engineering can happen offline by calling or even personally meeting the victim.
4. Brute force attack
If all else fails, password crackers have the brute force attack as a last resort. It basically involves trying all possible combinations until you hit the jackpot. However, password cracking tools allow to modify the attack and significantly reduce the time needed to check all variations. The user and his habits are the weak links again here.
If the attacker was able to brute force a password, he will assume the password has been re-used and try the same combination of login credentials on other online services. This is known as credential stuffing and is very popular in the age of data breaches.
5. Dictionary attack
A dictionary attack is a type of brute force attack that is often used together with other brute force attack types. It automatically checks if the password is not some often-used phrase like iloveyou by looking at the dictionary. The attacker might also add passwords from other leaked accounts. In such a scenario, the chance of a successful dictionary attack increases substantially.
If users were to choose strong passwords that contain not just one word, such attacks would quickly downgrade to a simple brute force attack. In case you use a password manager, then generating a random set of symbols is the best choice. And if you don’t, a long phrase made of at least five words is great too. Just don’t forget not to re-use it for every account.
6. Spidering
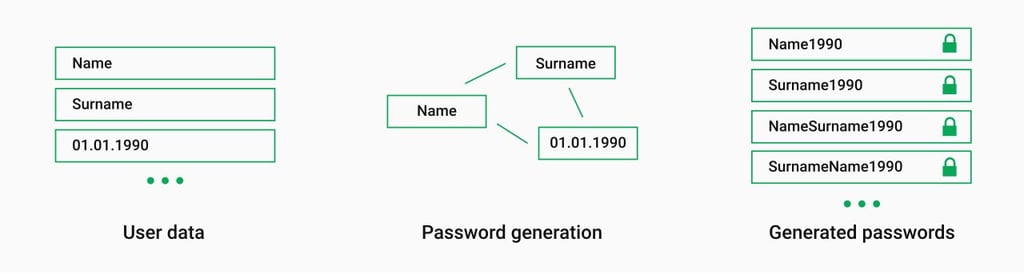
Spidering is a supplementary password cracking technique that helps with the above-mentioned brute force and dictionary attacks. It involves gathering information about the victim, usually a company, presuming that it uses some of that info for password creation. The goal is to create a word list that would help guess the password faster.
After checking the company’s website, social media, and other sources, one can come up with something like this:
- Founder name – Mark Zuckerberg
- Founder DOB – 1984 05 14
- Founder’s sister – Randi
- Founder’s other sister – Donna
- Company name – Facebook
- Headquarters – Menlo Park
- Company mission – Give people the power to build community and bring the world closer together
Now all you have to do is upload it to a proper password cracking tool and reap the benefits.
7. Guessing
While guessing is far from the most popular password cracking technique, it relates to business-oriented spidering above. Sometimes, the attacker doesn’t even have to gather information about the victim because trying some of the most popular passphrases is enough. If you recall using one or more of the most common passwords in the list below, I strongly recommend changing them now.
Some of the most common passwords worldwide:
- 123456
- 123456789
- qwerty
- password
- 12345
- qwerty123
- 1q2w3e
- 12345678
- 111111
- 1234567890
Even though the number of people who use simple or default passwords like password, qwerty, or 123456 is diminishing, many still love easy and memorable phrases. Those often include names of pets, lovers, or something related to the actual service, like its name (lowercase).
8. Rainbow table attack
As mentioned above, one of the first things criminals do when password cracking is getting the password in the form of a hash. Then they create a table of common passwords and their hashed versions and check if the one they want to crack matches any entries. Experienced hackers usually have a rainbow table that also involves leaked and previously cracked passwords, making it more effective.
Most often, rainbow tables have all possible passwords that make them extremely huge, taking up hundreds of GBs. On the other hand, they make the actual attack faster because most of the data is already there and you only need to compare it with the targeted hash-password. Luckily, most users can protect themselves from such attacks with large salts and key stretching, especially when using both.
If the salt is large enough, say 128-bit, two users with the same password will have unique hashes. This means that generating tables for all salts will take an astronomical amount of time. As for the key stretching, it increases the hashing time and limits the number of attempts that the attacker can make in given time.
Password cracking tools
No password cracking starts without proper tools. When cybercriminals have to guess from billions of combinations, some computational assistance is more than welcome. As always, each tool has its pros and cons.
Here is a list, in no particular order, of the most popular password cracking tools.
1. John the Ripper
Featured in many popular password cracking tools lists, John the Ripper is a free, open-source, command-based application. It’s available for Linux and macOS, while Windows and Android users get Hash Suite, developed by a contributor.
John the Ripper supports a massive list of different cipher and hash types. Some of those are:
- Unix, macOS, and Windows user passwords
- Web applications
- Database servers
- Network traffic captures
- Encrypted private keys
- Disks and filesystems
- Archives
- Documents
There’s also a Pro version with extra features and native packages for supported OS. Word lists used in password cracking are on sale, but free options are available as well.
2. Cain and Abel
Downloaded almost 2 million times from its official source, Cain and Abel used to be a popular tool for password cracking in the Windows XP/Windows 7 era. But contrary to John the Ripper, it uses GUI, making it instantly more user-friendly. That and the fact that it’s available on Windows only makes Cain and Abel a go-to tool for amateurs, also known as script kiddies.

This is a multi-purpose tool, capable of many different functions. Cain and Abel can act as a packet analyzer, record VoIP, analyze route protocols, or scan for wireless networks and retrieve their MAC addresses. If you already have the hash, this tool will offer a dictionary or brute force attack option. Cain and Abel can also display passwords that are hiding beneath the asterisks.
3. Ophcrack
Ophcrack is a free and open-source password cracking tool that specializes in rainbow table attacks. To be more precise, it cracks LM and NTLM hashes where the former addresses Windows XP and earlier OSs and the latter associates with Windows Vista and 7. NTLM is also available, to a certain degree, on Linux and FreeBSD. Both of these hash types are insecure – it’s possible to crack an NTLM hash in less than 3 hours with a fast computer.

As you can see in the screenshot above, it took Ophcrack merely six seconds to crack an 8-symbol password while using a rainbow table that includes letters, numbers, and uppercases. That’s even more variables than a mainstream password usually has.
This tool comes with free Windows XP/Vista/7 rainbow tables and a brute force attack feature for simple passwords. Ophcrack is available on Windows, macOS, and Linux.
4. THC Hydra
Arguably, the strongest point of THC Hydra is not the possible number of heads it can grow, but the sheer number of protocols it supports, which seems to be growing too. This is an open-source network login password cracking tool that works with Cisco AAA, FTP, HTTP-Proxy, IMAP, MySQL, Oracle SID, SMTP, SOCKS5, SSH, and Telnet, to name a few.
The methods available with THC Hydra include brute force and dictionary attacks while also using wordlists generated by other tools. This password cracker is known for its speed thanks to the multi-threaded combination testing. It can even run checks on different protocols simultaneously. THC Hydra is available on macOS and Linux, and for Windows requires a unix-based environment like WSL or Cygwin.
5. Hashcat
Positioning itself as the world’s fastest password cracker, Hashcat is a free open-source tool that’s available on Windows, macOS, and Linux. It offers a number of techniques, from simple brute force attack to hybrid mask with wordlist.

Hashcat can utilize both your CPU and GPU, even at the same time. This makes cracking multiple hashes simultaneously much faster. But what makes this tool truly universal is the number of supported hash types. Hashcat can decipher MD5, SHA3-512, ChaCha20, PBKDF2, Kerberos 5, 1Password, LastPass, KeePass, and many more. In fact, it supports over 300 hash types.
But before cybercriminals can start cracking, they need to have the password hash first. Here are some of the most popular tools for getting hash:
- Mimikatz. Known as a password audit and recovery app, Mimikatz can also be used for malign hash retrieval. In fact, it might as well extract plaintext passwords or PIN codes.

- Wireshark. Wireshark enables packet sniffing. It is an award-winning packet analyzer used not only by malicious hackers but also by business and governmental institutions.

- Metasploit. This is a popular penetration testing framework. Designed for security professionals, Metasploit can also be used by cybercriminals to retrieve password hashes.

How to create a strong password?
No matter how good your memory or your password manager is, failing to create a good password will lead to undesired consequences. As discussed in this article, password cracking tools can decipher weak passwords in days, if not hours. That’s why I feel obliged to remind you of some of the key tips for coming up with a strong passphrase:
- Length. As it often is, length is the most important factor.
- Combine letters, numbers, and special characters. This greatly increases the number of possible combinations.
- Do not re-use. Even if your password is strong in theory, re-using it will leave you vulnerable.
- Avoid easy-to-guess phrases. A word that’s in the dictionary, on your pet’s collar or on your license plate is a big NO.
If you would like to learn more about creating good passwords, consider checking out our How to create a strong password article. You can also try our password generator that will help you to come up with safe passwords.
If you don't feel confident enough about creating multiple strong passwords, getting a password manager, like NordPass, won't let you worry about that ever again. NordPass generates unshakable passwords and uses powerful encryption.
Generate strong passwords with NordPassIs password cracking illegal?
There’s no clear cut answer to this. For starters, all password cracking tools described above are perfectly legal. That’s because they play a key role in checking for vulnerabilities and can also help recover a lost password. What’s more, such tools help law enforcement fight crime. So as it often is, password cracking can help both the good and the bad cause.
As to the password cracking as an activity, it depends on two factors. One, the hacker doesn’t have the authority to access that particular data. Two, the goal is to steal, damage, or otherwise misuse the data. Even if only one of these factors is present, a cybercriminal will most likely receive a punishment, ranging from a fine to multi-year imprisonment.
To sum up, if there’s no bug bounty, no agreement to do penetration testing, and no request to help recover a lost password, cracking is illegal.
Bottom line
Password cracking is easier than most users think. There are plenty of free tools and some of them are easy enough even for novice crackers. There’s also more than one password cracking technique to try. Starting with a simple brute force attack and moving on to sophisticated methods that combine different techniques, password cracking is evolving every day.
The best defense against password cracking is using a strong password. Using enough symbols and different characters ensures that even the fastest computer won’t crack your account in this lifetime. And since remembering multiple strong passwords is unlikely, the best bet is to use a reliable password manager, like NordPass. Two-factor authentication is still a significant challenge for any hacker, so adding a fingerprint or face ID will keep your data safe, at least for the foreseeable future.





