
Since their emergence in the late 1990s, Denial of Service (DDoS) attacks continue to be a mainstay for threat actors. As 2024 looms, these invisible onslaughts continue to threaten system stability across a wide range of government institutions, industries, and organizations, casting a shadow of uncertainty on the ability to maintain highly secure and connected environments.
Denial of service attacks, including their distributed counterparts, are some of the oldest cyberweapons around. They've been used as a primary attack of choice for cybercriminals since approximately 1996, with the first impact hitting internet service provider Panix1. Cisco predicts that nearly 15 million DDoS attacks will occur before 2023 concludes, making it one of the most widely experienced and utilized attacks seen year over year.
Questions arise, such as, “How are these attacks still successful in the days of sophisticated web applications and network traffic filtering services like Cloudflare or Imperva WAF?” Additional research conducted in Q2 2023 by Black Lotus – the threat intelligence arm of Lumen Technologies, provides a concerning perspective into why this antiquated attack remains highly successful nearly three decades after its emergence – the continued evolution of multi-vector DDoS Attacks. Showcasing several government and educational institution examples from Europe that occurred across September 2023, this article will delve into approaches used within Multi-Vector DDoS attacks, defensive considerations, and some of the threat actors behind these attacks.
Between September 7th and 23rd, 2023, several consecutive DDoS attacks rocked the transport and communications agency Traficom, impacting the ability of the Finnish Government to manage its driver licensing operations and issuance of business licenses. Despite taking action to mitigate these attacks from occurring, Traficom has been repeatedly victimized by cyber disruptions. They required users to work through 3rd party, non-government services like insurance agencies while Traficom services were fully restored. Traficom later implicated Russian-based cybercrime outfit “NoName” as the Advanced Persistent Threat (APT) actor behind the attacks.
Similar DDoS attacks were also reported in late September, briefly impacting the Thomas Moore University of Applied Sciences in Antwerp, Belgium, the Elron Train ticketing system in Estonia, and the Progressive Party of Slovakia’s primary website. These latest examples highlight just how popular DDoS attacks remain and their effectiveness in impacting larger state-run entities. However, it's important to understand why multi-vector DDoS attacks are breaking through modern-day cyber defenses.
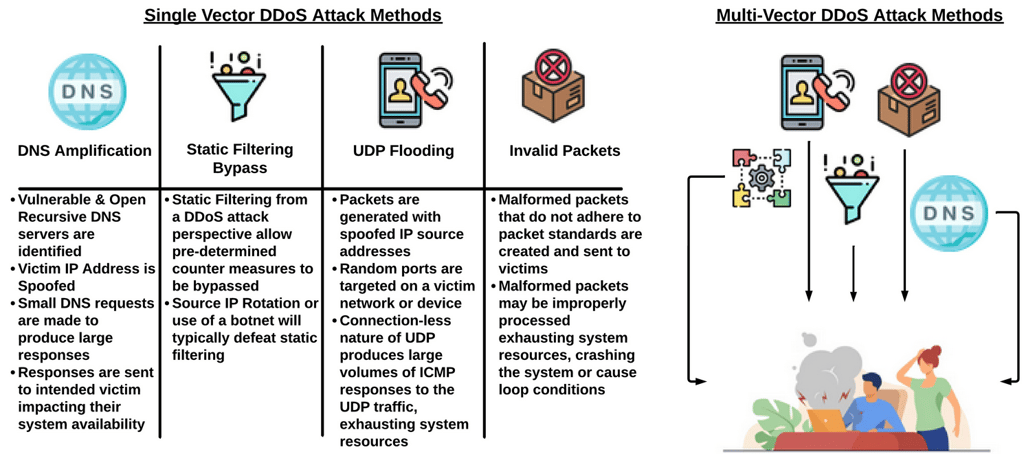
Single vs multi-vector DDoS attacks
Traditional single-vector DDoS attacks such as ICMP, HTTP, or UDP flooding attacks focus on a specific application or device vulnerability, exploiting smaller numbers of network protocols. Their straightforward manner, such as a sudden traffic surge, makes them easier to detect and block. Multi-vector DDoS attacks are an entirely different beast to defend against, as attackers will carefully plan their campaigns over time. Multi-vector DDoS campaigns are meticulously orchestrated, blending multiple single-vector attack strategies together while leveraging evasion techniques to confuse and overwhelm defenders. The infographic below summarizes common single-vector DDoS attack or bypass strategies and then depicts how these single-vector attack strategies may be combined into a comprehensive campaign, including IP fragmentation that is designed to overwhelm, distract, or circumvent standard DDoS mitigation strategies.
DDoS impact and notable threat actors
Research performed in Q2 2023 by Lumen’s Black Lotus Labs reflects average multi-vector DDoS attacks lasting around two hours (an increase of nearly 30% from Q1), with the longest sustained attack occurring for a full 7 days.
When these attacks successfully disrupt organizations, the impact typically includes a mixed-bag factor of lost revenue per hour, total mitigation costs, and irreclaimable reputational loss. Extrapolating some of Lumen’s Q2 impact model predictions, businesses with a strong online presence (i.e., telecom providers, hosting providers, etc.), which generate $100 million in annual revenue, have under 500 users and employ small cybersecurity teams may experience several dozen DDoS attacks per year. These attacks can last, on average, around eight hours and cost upwards of $5 million annually. Lumen provides a threat calculator tool to help organizations determine their potential impact or losses stemming from a successful DDoS attack.
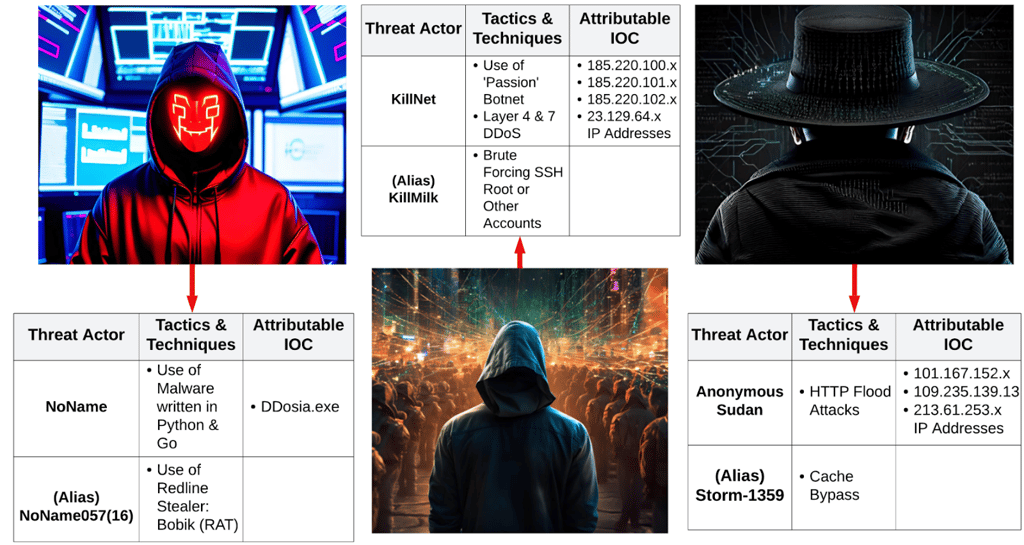
Notable cyber threat actors perpetuating multi-vector DDoS include Russian Federation syndicates such as NoName, Killnet, and Anonymous Sudan. These threat actors often work in close collaboration with each other spreading pro-Russian propaganda and attacking nation-states or organizations supporting Ukrainian efforts to engage in military operations against Russia. Other splinter cells of these groups, such as Zarya and Tesla Botnet, will also actively broker malware on the Dark Web, provide direct DDoS attack assistance, or perform broader recruitment efforts. More information is available below depicting specific tactics, techniques, procedures, and IOCs attributable to these DDoS-focused threat actors:T
Multi-vector DDoS attacks are not just a concern for Europe either, as these attacks are also seeing an increase across North America. Several reports across late September for sustained DDoS and other availability-based cybersecurity incidents were observed impacting the Canadian Armed Forces website, an Ottawa hospital, and the Maines County Courthouse in Missouri, USA, on September 25th. In these instances, different threat actors were either alleged or not provided. The attacks primarily impacted website availability for core governmental or critical infrastructure operations for several hours to days, but in all cases, services were restored.
Defensive Considerations
Organizations aiming to thwart multi-vector DDoS attacks should prioritize a holistic, layered defense strategy. First, an organization will need to perform a risk assessment against its network architecture to prioritize critical assets prone to DDoS attacks. Current control capabilities may require augmentation to successfully thwart DDoS attacks and typically consist of the following considerations:
- Investing in robust cloud-based DDoS protection services that can scale rapidly, absorbing large traffic volumes
- Employing a web application firewall (WAF) that can filter out malicious traffic and identify patterns indicative of evolving threats
- Performing continuous monitoring of network traffic to identify and proactively respond to anomalies by auto-adjusting firewall rules or activating traffic scrubbing solutions
- Ensuring infrastructure is resilient and diversified, minimizing the risk of any single point of failure
- Fostering partnerships with ISPs and other service providers to enable additional layers of defense during a DDoS onslaught, such as black or sinkhole capabilities.
As seen in the above examples, multi-vector DDoS provides a constant reminder that these archaic attacks can remain highly successful even in our modern, evolved technology paradigm. The rise of multi-vector DDoS attacks presents both a formidable challenge and an opportunity for organizations to fortify their digital defenses.
Threat actors like Killnet, Anonymous Sudan, and NoName may pose significant risks, but by implementing the defensive strategies discussed above, organizations can bolster their resilience and avoid unnecessary impacts. Beyond mere survival, embracing these cybersecurity measures can empower organizations to not only safeguard their assets and data but also pave the way for innovation and growth in the digital landscape.
By staying vigilant, adaptive, and informed, organizations can not only weather the storm of multi-vector DDoS attacks but also emerge stronger, more secure, and better positioned to achieve their strategic objectives in an increasingly connected world.






Your email address will not be published. Required fields are markedmarked