
Hacktivists devote a lot of time scouring the internet for vulnerable devices. The traditional way can take anywhere from minutes to days. Most hackers nowadays search for easy targets for faster results. It’s almost like playing the lottery. With Shodan, much of the network reconnaissance is already done for you. The only thing left is the intrusion itself.
We didn’t have power open source intelligence (OSINT) tools like this back in the day. We had tools for everything, but for quicker results and less time behind the command line, we had scripts that provided autonomy, which had lots of dependencies to maximize our results.
This comes with plenty of risks. After all, the more packets you have to send, the more network noise you make. This translates to Red Team attacks not being stealthy enough to not go unnoticed during security audits such as logging by intrusion detection systems.
A brief overview
I’ve been floating around various hacking circles for a few years now, observing trends and learning what special ingredients are used to obtain intrusions. This is important to know because groups that cause newsworthy cyberattacks often have a method for finding interesting systems. That method is Shodan.
In a nutshell, Shodan is a search engine for internet-connected devices. This means users can find and analyze devices across the internet. It can detect data leaks to the cloud, determine whether a website is being used in a phishing campaign, and provide monitoring capabilities for your own connected devices on the web.
It can publish network shares associated with a domain, user account information, snapshots from account login prompts, and subdomains. It can also expose credential policies for default credentials from banner-grabbing and publish them in searchable plain text. The list of functions is extensive.
Shodan spiders across the entirety of the internet at least once a week, which means the scans are performed asynchronously, so the results are not in real time. However, users can opt for on-demand scanning through their API.
Like anything that can be used ethically, it also possesses what I like to call ‘dark side’ capabilities, which, of course, depend on the user's intent.
Bending ethics
As a network security researcher and former blackhat hacker, the entire hacking landscape fascinates me. Consequently, the hunger to learn enraptures me, which compels me to learn as much as I can, especially when following the trends or learning about obscure ways hackers discover their illicit access.
Naturally, I spend a lot of time poking around Shodan, which has a vast array of filters for narrowing down specific information.
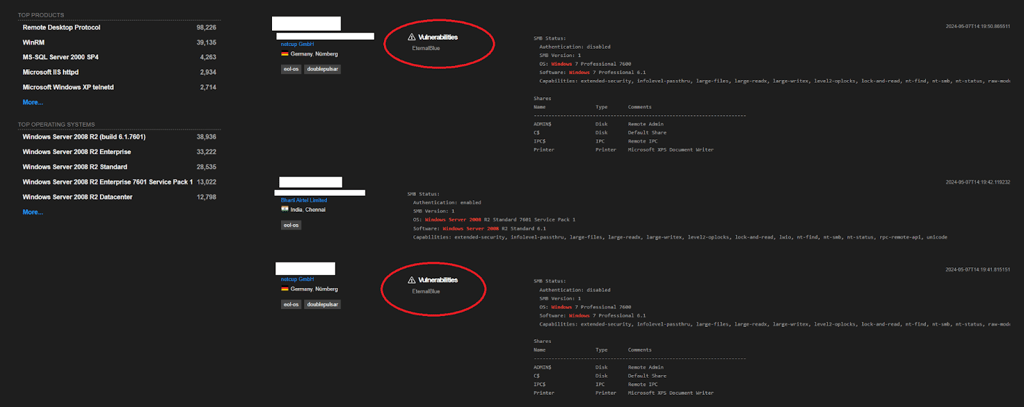
For example, if I wanted to specifically search for Windows systems that are vulnerable to the BlueKeep (CVE-2019-0708) or EternalBlue (CVE-2017-0144) Remote Code Execution (RCE) vulnerability, Shodan would help me leverage this vulnerability by giving me a list of affected devices – with an Academic or Small Business API subscription, of course.
That's where a hacker doesn’t shrug and move on. While some filters require a paid subscription, there’s a workaround.
For example, instead of using the vulnerability search filter to find Windows devices vulnerable to the BlueKeep and EternalBlue vulnerabilities, an attacker who knows which operating systems are exploitable can simply use the OS search filter to search os:"Windows 7, Windows Server 2003, Windows Server 2008, Windows Server 2008 R2, Windows Vista, Windows XP".
It's important to remember that Shodan’s scan results are asynchronous and might not reflect the present state of a system it reports. Oftentimes because hackers are constantly digging through this massive trove of Internet of Things (IoT) and attacking low-hanging fruit, those might find themselves patched while still reporting them as vulnerable until it is updated.
Revisiting the ethics of OpRussia and OpIsrael
Since the onset of the Russia vs Ukrainian war, which began on February 24th, 2022, and the Israel vs Palestine war, which started on October 23rd, 2024, the two foremost devices being targeted by information supplemented by Shodan have been industrial controls and CCTV/IP cameras.
While hacktivists take sides in respective wars, the tools are largely the same. Shodan is a prominent tool for leveraging cyber intelligence, especially its API, which allocates search results into an easy, shareable format.
Enumerating devices by using city or zip code filters helps narrow down potential attack surfaces. In this way, hacktivists have been able to assist Ukrainian civilians and soldiers alike by providing remote eyes in hostile locations to coordinate secure movement. Similarly, camera systems have been sabotaged in key locations to prevent the watchful eyes of enemies.
This exceptionally powerful search engine has also been used to identify and map critical industrial control systems, such as Modbus devices, which are often used in the energy and transportation industries.
For example, the control panel for Russia’s Metrospetstekhnika’s IT system for their railway infrastructure was discoverable through Shodan. Consequently, in the Spring of 2022, the hacktivist group known as GhostSec and a member of the hacker conglomerate known as The Five Families took Russia’s entire train system offline in their support of Ukraine and succeeded in preventing Russia from moving military supplies from Belarus to Russia.
As the hacktivist landscape becomes increasingly focused on geopolitical cyber warfare, hackers have developed the mentality of devising new ways to interfere with military operations on both sides of every war. This is inevitable, and as a consequence, the hacktivist group Anonymous finds itself divided against itself.
Civilian operations like these have the potential to save or destroy lives, depending on which side of the war you choose. In the case above, undeliverable military assets meant that they couldn’t be used to aid Russia’s advancement, which also disrupted the movement of critical assets, schedules, and other such plans involving transport by rail system.
Similarly, in June 2022, GhostSec’s attack against the Gysinoozerskaya hydroelectric power plant in Russia, which resulted in a maxi-explosion, is also attributed to discoverable Modbus devices being searchable on Shodan. This was performed with careful insight so as not to have any opportunity to cause any injury or casualties.
Others, however, are not concerned with the risk of causing a threat to life and limb.
It is important to note that Shodan does not provide the recipe for the intrusions, but rather, the information it returns from user-defined searches can be used to explore viable attack vectors. As I end here, you must understand that there is no removing the hacker from the equation.
We exist to exist. Hacktivists exist because the Powers-That-Be are limited in power and interest to defend the people in cyberspace. Hacktivism will never cease to exist, but neither should our ethics. Ethics are the most under-represented element in hacktivism operations when it should be at the very forefront.
We are not bound by diplomacy. However, we should unite under the banner of a set of ethics since cyberattacks nowadays are becoming increasingly dangerous to public health and safety.
GhostSec’s leader, Sebastian Dante Alexander offered these final thoughts: “When it comes to hacking industrial controls play it right, don’t rush the learning process so you can cause some damage. You may end up worse than expected, pick the right targets, make sure you’re ready, and strategize it right.”
If hacking is your superpower, then hack responsibly.






Your email address will not be published. Required fields are markedmarked