
New research shows that Apple and Starlink WiFi-based Positioning Systems (WPS) can be abused to create a global privacy threat, especially in war zones.
WPS technology uses WiFi signals to determine the physical location of a device, such as a smartphone or a tablet. It operates by triangulating the device's position based on the known locations of nearby WiFi access points and the strength of the signal.
Periodically, mobile devices send their locations, determined via GPS and/or cellular towers, along with nearby Basic Service Set Identifiers (BSSIDs). This combination of data enables these devices to accurately determine their location within a few feet or meters.
Apple collects this location data on server to give devices a crowdsourced, low-power alternative to constantly requesting global positioning system (GPS) coordinates.
Researchers at the University of Maryland conducted an attack using publicly available data from Apple to gather a worldwide snapshot of WiFi BSSID geolocations in just a few days and perform mass surveillance of users' WiFi access points virtually anywhere in the world.
The researchers warned that the attack model they tried required only minimal technical knowledge and could be carried out by individuals with consumer-grade hardware.
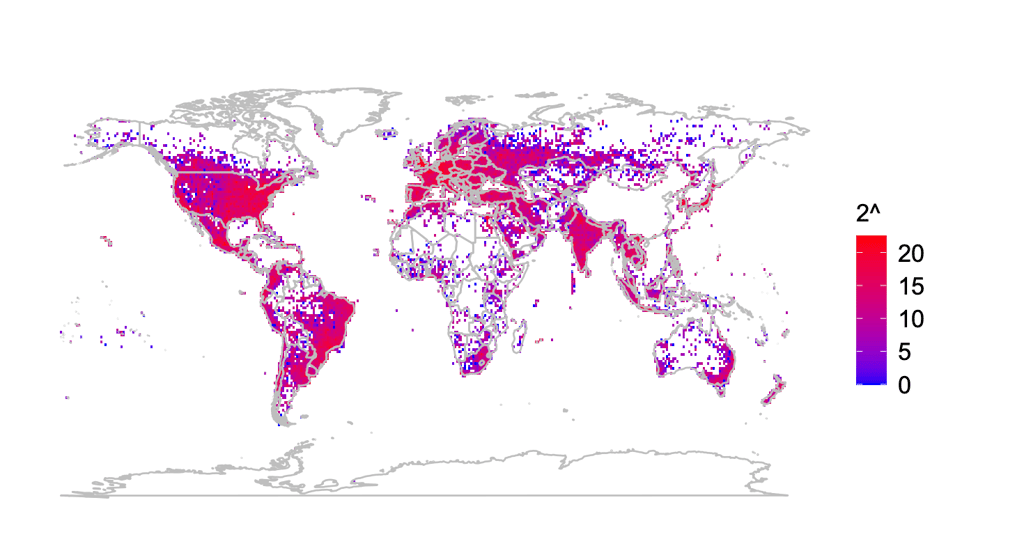
During a year of research, the team determined the precise locations of over two billion BSSIDs worldwide.
The researchers were able to determine the movement of travel routers, such as GL.iNet devices, which, according to the team, pose “a grave threat to individuals who wish to not be tracked.”
The tracking becomes extremely sensitive in the conflict zones. Researchers analyzed war zones in Ukraine and identified at least 3,722 satellite-based broadband service Starlink terminals, exposing pre-deployment sites, and military movement.
Compounding the issue raised by the researchers, users whose devices were tracked never opted into Apple’s WPS. Simply being within the WiFi range of an Apple device could result in a device's location and movements being publicly and widely available.
The team disclosed their findings to Apple and Google, both of which operate their own WPS, as well as two prominent manufacturers – SpaceX and GL.iNet.
In March 2024, Apple updated its website to indicate that individuals can opt out of having their wireless access points' locations collected and shared by Apple.
Users can opt out by adding "_nomap" to the end of the WiFi access point's name (SSID). Appending "_nomap" to your WiFi network name also prevents Google from indexing your location.






Your email address will not be published. Required fields are markedmarked