
Criminals continue to take advantage of the ease of creating PayPal accounts and generating invoices to send phishing emails.
PayPal users should be careful and not fall for phishing scams thriving on the platform. Last year a new campaign was discovered by researchers at Avanan, where attackers sent phishing emails and malicious invoices directly from PayPal.
The method was different from the usual attacks that spoofed PayPal, as it was incredibly difficult for both email security services and end-users to detect and prevent malicious activity.
Uses PayPal’s tools for invoice creation
Threat actors exploit free and easy-to-create PayPal accounts and the platform's tools dedicated to creating professional-looking invoices to generate malicious invoices and messages. Using these tools, threat actors can easily impersonate family members or employers.
Emails sent as part of this attack campaign are not inherently malicious, as many legitimate invoices are sent via PayPal daily. These emails are sent directly from PayPal and can pass several checks, including SPF, DKIM, and DMARC, among others. As the emails are coming from [email protected], they look legitimate, making it hard for users to spot discrepancies.
“PayPal and QuickBooks are particularly clever since they are often used for business invoices,” said Avanan, adding that what makes the scam effective is static email “allow lists” that permit content from such reputable providers to go directly to an inbox.
“Trusted websites like PayPal often make the cut, even if it is an oft-impersonated brand,” said Avanan. “What makes this attack scary is that the phishing invoices are created and sent through PayPal. That makes it [seem] more legitimate to the security service and to the end-user.”
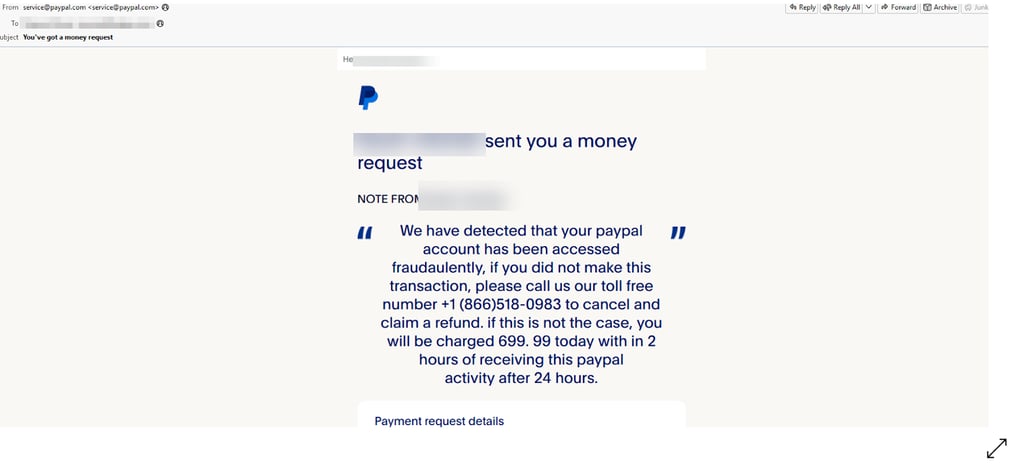
Researchers provided one example of how a malicious email looks: the email comes directly from PayPal, and the sender's address is [email protected].
The email contains alarming claims of fraudulent activity on the recipient's account. The emails threaten that if the recipient fails to take immediate action by calling the listed phone number, they will be charged a significant amount of money, such as $699.99.
However, upon closer inspection, the body of the email may contain inconsistent grammar and spelling and a phone number that is not affiliated with PayPal.
These errors are a potential clue to eagle-eyed users that something is amiss. Despite this, the scammers hope to entice victims to call the phone number or click on a link for more information, thereby providing an opportunity to obtain personal details and execute further attacks.
How to stay safe?
Traditional email security solutions and next-gen solutions would not be effective in detecting such scams, and advanced AI and ML trained on an enormous database would be required to spot this type of malicious email.
To avoid falling victim to these attacks, users are advised to check accounts and Google unfamiliar services before calling them.
Additionally, they should implement advanced security that looks at more than one indicator to determine whether an email is clean. It's also crucial to encourage users to ask IT if they need clarification on the legitimacy of an email.
PayPal experienced a data breach
In December last year, PayPal experienced a data breach that affected thousands of users. Investigators say an unknown third party was able to gain access to the personal accounts using a hacking technique known as credential stuffing. They claimed the acquired login credentials were not taken from any PayPal systems.
PayPal urged customers to change the passwords for any account using the same login credentials as their PayPal account and, most importantly, to enable 2-step verification on their account.






Your email address will not be published. Required fields are markedmarked