
Direct Trading Technologies, an international fintech company, jeopardized over 300K traders by leaking their sensitive data and trading activity, thereby putting them at risk of an account takeover.
On October 27th, the Cybernews research team discovered a misconfigured web server with backups and development code references allegedly belonging to the fintech company Direct Trading Technologies.
Direct Trading Technologies (DTT) is an international fintech company offering trading platforms for stocks, forex, precious metals, energies, indices, Contracts for Difference (CFDs), and cryptocurrencies. Also, DTT offers white-label services for fintech solutions.

While the main clientele is based in Saudi Arabia, the company has offices in the UK, Lithuania, UAE, Kuwait, Colombia, Turkey, Bahrain, Lebanon, and the Republic of Vanuatu.
The discovered directory included multiple database backups, each holding a significant amount of sensitive information about the company's users and partners. The leak poses a variety of risks, expanding from identity theft to takeover and cashing-out accounts of traders.
Cybernews contacted the company with our findings. While the problem was fixed, an official response from the company is still yet to be received.
Sensitive data leaked
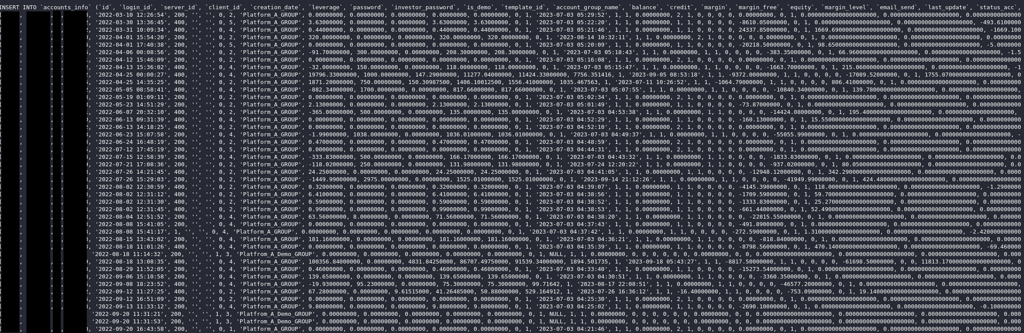
The leaked data included the trading activity of over 300,000 users spanning the past six years, along with names, email addresses, emails sent by the company, and IP addresses.
Users holding the company’s email addresses, potentially the employees, had their passwords exposed in plaintext. Hashed passwords to access user accounts on the DTT trading platform were also leaked. Some clients had their home addresses, phone numbers, and partial credit card details exposed.
Full list of leaked data:
- Trading account activity
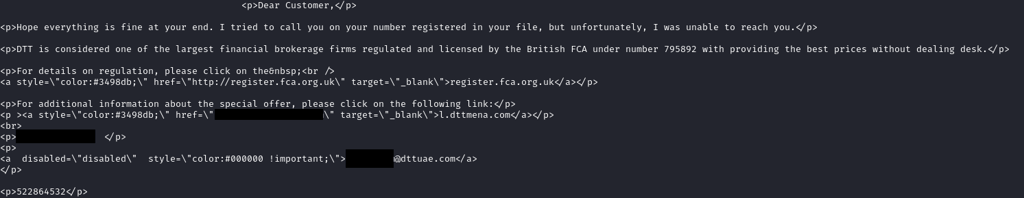
- Contents of emails sent by DTT
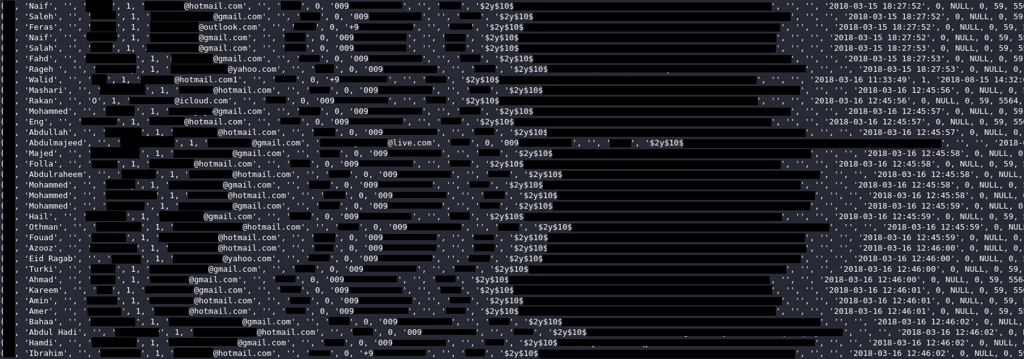
- User IP addresses, emails, usernames, and plaintext passwords
- Notes on outreach calls
- Names
- Email addresses
- Phone numbers
- Home addresses
- Hashed passwords
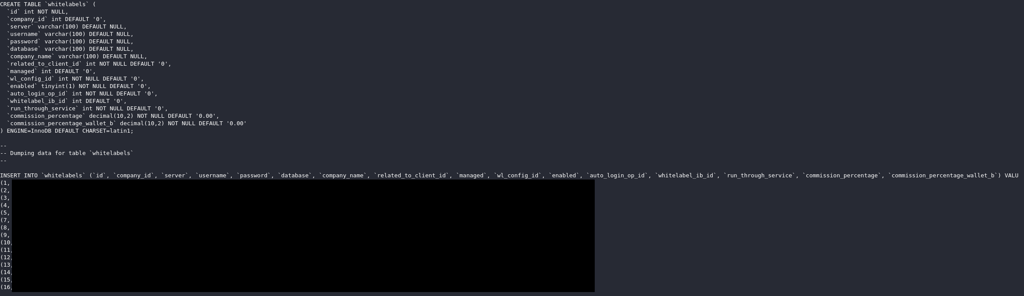
- Database endpoints and plaintext credentials of white-label customers (endpoints were protected by IP whitelists)
- Locations where KYC documents are stored, filenames, types, expiration dates, and other metadata
While Know Your Customer (KYC) documents were not exposed, the leaked files revealed the locations where the documents are stored and other metadata.
The credentials of clients using the white-label service were exposed in plaintext, along with details of database locations and negotiated commission percentages.
The leaked data also contained internal comments from the company's outreach team regarding the calls they made. The file shows that some clients are called “idiots” in the company’s system.

Potential takeover of financial accounts
With the fintech industry experiencing rapid growth, this leak stands as a clear reminder of the critical role of robust cybersecurity measures. Fintech companies manage and store exceptionally sensitive customer data.
Traders are prime targets for threat actors because their accounts hold significant value. Attackers can take over high-value accounts to cash them out or misuse stolen accounts, especially the ones that have already passed the KYC process.
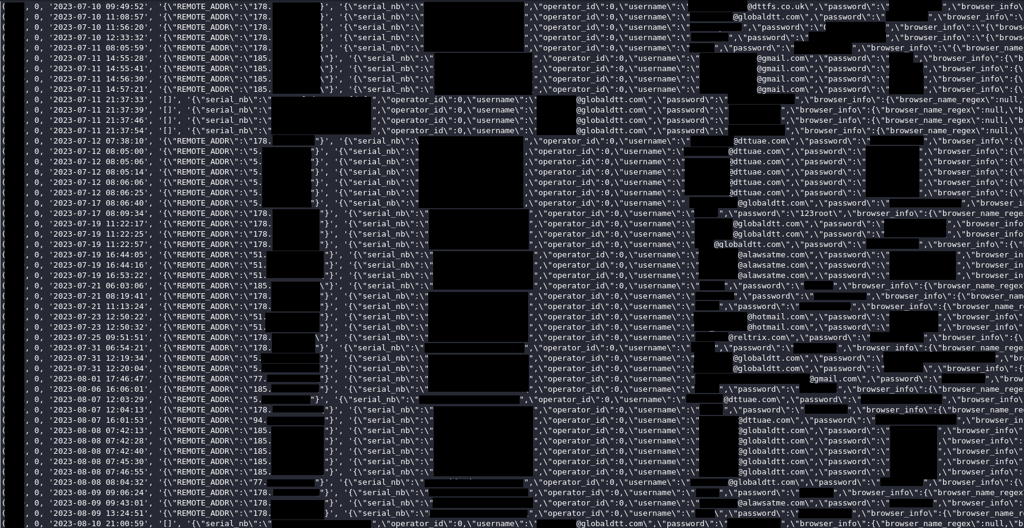
With leaked data from a trading platform, attackers have ample information to launch various attacks against affected customers, including account takeover, phishing, identity theft, and malware exploits (owing to leaked IPs), as well as credential stuffing attacks.
As the company offers a white-label service to numerous other firms and stores credentials for clients’ databases, the leak could have posed a further threat. However, accessing these databases would have added an extra step for attackers, requiring them to compromise a trusted network.






Your email address will not be published. Required fields are markedmarked