
Before you entrust your private data to any app, ask yourself: who’s really on the other side of the screen? Research reveals that the Apple iOS app used to securely store private data has instead left it accessible to anyone on the internet.
- iOS app Photo Vault, dedicated to storing and protecting private user data, exposed user passwords, notes, and photo information to anyone on the internet
- The leak was caused by a passwordless Firebase database
- Attackers could track the data users upload in real-time
- The iPhone app also leaked other sensitive secrets that could facilitate further cyberattacks
- After the disclosure, the developer of the app secured access to user data
Picture this: you hand your phone over for repairs, accidentally leave it behind in a coffee shop, or have to deal with a nosy partner – the last thing you want is for someone to dig through your private photos, notes, and files. Some users turn to apps that can lock it all away in the cloud, safe from prying eyes.
For thousands of users, one such app, Photo Vault, seemed like the perfect solution – a digital lockbox promising to keep intimate photos, sensitive notes, and private passwords hidden behind layers of security.
Face ID, Touch ID, encryption – it all sounded airtight. But in reality, the app wasn’t nearly as private as it claimed to be. Cybernews research has uncovered a massive security lapse that left Photo Vault’s Firebase database completely exposed.
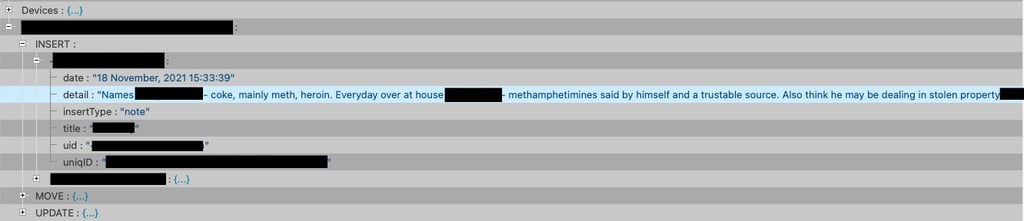
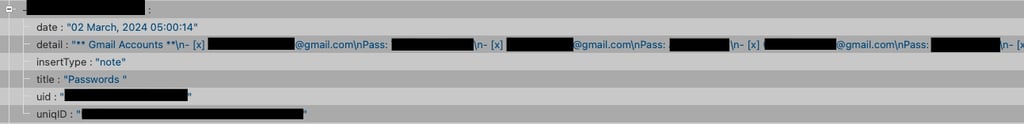
The leak exposed everything – from folder and file names to user email addresses, plaintext passwords, and even supposedly “secure” notes – leaving it all accessible online to anyone with enough know-how to find it. The photo metadata hints that plenty of the photos might be intimate.
This leak is extremely dangerous, as hackers can set up scrapers to constantly suck up sensitive data from the Firebase instance, getting real-time access to fresh passwords and other private info as soon as it's uploaded. To make matters worse, attackers could exploit passwords users upload to the vault to hijack their accounts.
The company behind Photo Vault, a developer called Brain Craft, operates out of Bangladesh and boasts a portfolio of over 20 apps, claiming a total of 20 million downloads and 15 million users. Among them, Photo Vault alone was downloaded 72,000 times.
After discovering the leak, Cybernews contacted Brain Craft, prompting them to secure access to the exposed database. However, the company has yet to provide an official comment on the leak.

What did the iOS app leak?
- 56 password entries
- 81 notes, some of which were also titled “Passwords”
- Metadata for 17 thousand photo albums created and stored by users

Firebase is often used as a temporary database – a staging ground for data that gets synced with a permanent storage system once it reaches a certain threshold. When that Firebase instance gets flooded, old data gets wiped.
But not before hackers can swoop in and set up a scraper to monitor every change, copying fresh passwords and private info in real-time as it’s uploaded – from passwords and notes to file and folder metadata in the cloud.
If hackers get their hands on this data, they can gain insight into what's inside users’ “private” vaults, hijack accounts, and siphon off even more sensitive data from linked services like Facebook or Dropbox.
While user photos stored in the vault are inaccessible, the album and file names were still out there, leaking personal details. People tend to give their folders descriptive names to keep things organized – which also makes it easier for attackers to piece together someone’s private life when they cross-reference it with other data.
“Some of these folder names were descriptive enough to identify criminal activity such as hacking into other people's accounts to access sensitive data stored within,” said Cybernews researcher Aras Nazarovas.
“Since multiple users used this service to also store passwords and notes, it is possible that an attacker could use this information to gain unauthorized access to the private vaults by performing credential stuffing attacks,” he added.

The safety app is unsafe by design
The app didn’t just fail to protect user data – it exposed sensitive information, commonly known as secrets, directly in the client-side code. These exposed secrets are some of the top 10 most leaked secrets among iOS apps.
Cybersecurity experts warn that leaving API keys, credentials, and other sensitive information in the published app’s code – or, in other words, "hardcoding" them – is a dangerous practice that could open the door to attackers.
What secrets were exposed?
- API Key
- Client ID
- Google App ID
- Project ID
- Reversed Client ID
- Storage bucket
- GAD Application Identifier
- Facebook App ID
- Database URL
This is an open invitation to wreak havoc for any threat actor with a little technical skill. By simply enumerating the infrastructure, attackers could identify vulnerable services, abuse them for unauthorized purposes, or worse, harvest sensitive user data directly from the app.
If any authentication secrets had also been exposed, hackers could have taken control of entire services connected to the app.
This could allow them to do everything from sending spam through the app’s infrastructure to leveraging it for nefarious purposes like harvesting user data or even conducting fraudulent activities.
iOS apps are leaking secrets, and it’s a serious problem
The leak was uncovered during a large-scale investigation by Cybernews. The researchers downloaded 156,000 iOS apps, around 8% of all apps on the Apple Store, to discover that app developers are leaving plaintext credentials in the application code accessible to anyone.
The findings revealed staggering numbers: 71% of the analyzed apps leak at least one secret, with an average app's code exposing 5.2 secrets.
Recently, other Cybernews research revealed that popular iOS dating apps leaked extremely dangerous secrets. They granted access to storage buckets with nearly 1.5 million user photos, including photos removed for rule violations and private photos sent through direct messages.
Another finding revealed that an iOS GPS tracker app was leaking user phone numbers and GPS location data, making stalkers' dreams come true.
Disclosure timeline:
Leak discovered: January 7th, 2025
Initial disclosure: January 15th,2025
Leak closed: February 3rd, 2025






Your email address will not be published. Required fields are markedmarked