
As the war continues raging in Ukraine, Russia maintains pressure by launching a series of cyberattacks and hijacking legitimate penetration testing tools to destroy or gain control over targeted systems.
"With Ukraine being targeted by a variety of cyberattacks, we can clearly see that government assets, critical infrastructure, media, and private sector organizations are highly lucrative targets for attackers," - Pawel Knapczyk, Security Research Manager at Trustwave SpiderLabs, said in a blog post.
Cobalt Strike, primarily designed for red teams, is one of the tools actively abused by attackers for downloading and executing malicious payloads.
Knapczyk noted that, despite best efforts to cover their tracks, Russian threat actors leave some traces behind, eliminating any doubt about the Kremlin's involvement in the ongoing cyberwar against Ukraine.
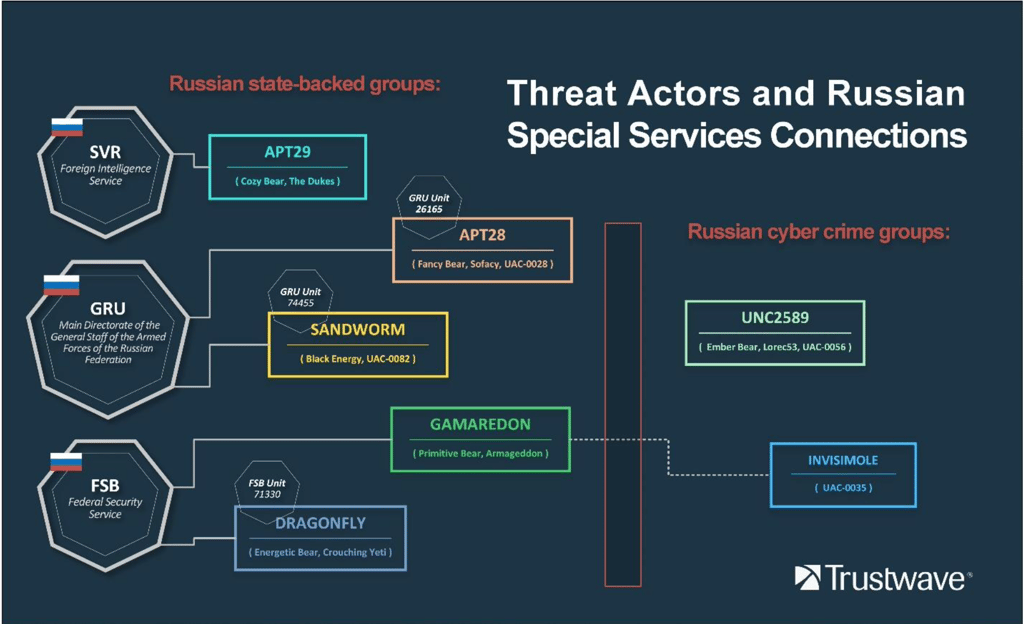
For example, Cozy Bear (APT28, the Dukes) has ties to the Russian Foreign Intelligence Service. Fancy Bear (Sofacy) and Sandworm (Black Energy) were both traced to the Main Directorate of the General Staff of the Armed Forces of the Russian Federation (Former GRU.)
Dragonfly (Energetic Bear or Crouching Yeti), as well as Gamaredon (Primitive Bear or Armageddon,) were traced to the Russian Federal Security Service (FSB).
"Other actively involved threat actors such as UNC2589, also known as Ember Bear or Lorec53, and InvisiMole do not present such clear ties with Russian special services. However, as published by ESET researchers, InvisiMole was found to be using server infrastructure operated by Gamaredon," Knapczyk said.
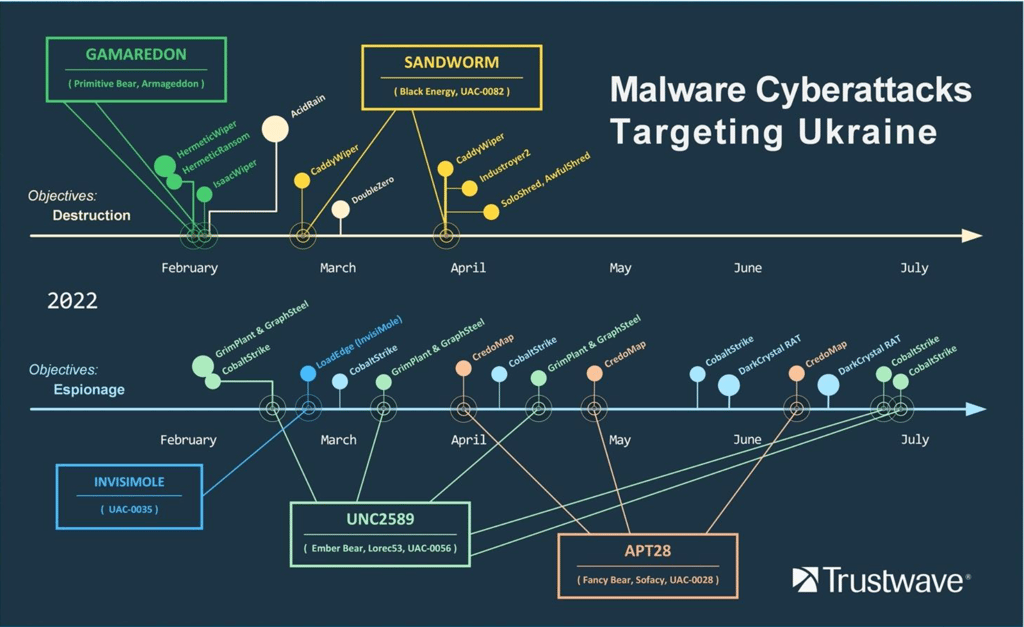
Trustwave SpiderLabs highlighted two lines of attacks differentiated by the attacker's objectives: destructive attacks meant to destroy the data and render targeted systems inoperable, and espionage attacks designed to establish a foothold and exfiltrate data from targeted systems.






Your email address will not be published. Required fields are markedmarked