
Cybercriminals are impersonating the Social Security Administration (SSA) to pressure vulnerable US citizens and migrant workers into revealing their social security numbers.
Social engineering watchdog INKY revealed the findings in its latest “fresh phish” report, which found PDF documents used to spoof authentic communications from the SSA sent to citizens, permanent residents, and temporary workers.
This particular campaign involved a two-pronged attack, with victims lured into calling bogus support numbers in what is known as a “vishing” or voice-phishing scam. Threat actors aimed to persuade victims to part with their social security numbers (SSNs) – valuable data that can be used to facilitate myriad other online crimes in the US.
“Americans have plenty to worry about these days, and at the top of the list is money, government, and the future – creating a perfect storm of anxiety,” said INKY. “On their own, each of these topics has the power to create a pretty hefty amount – combine them, however, and you have the perfect recipe for phishing mayhem.”
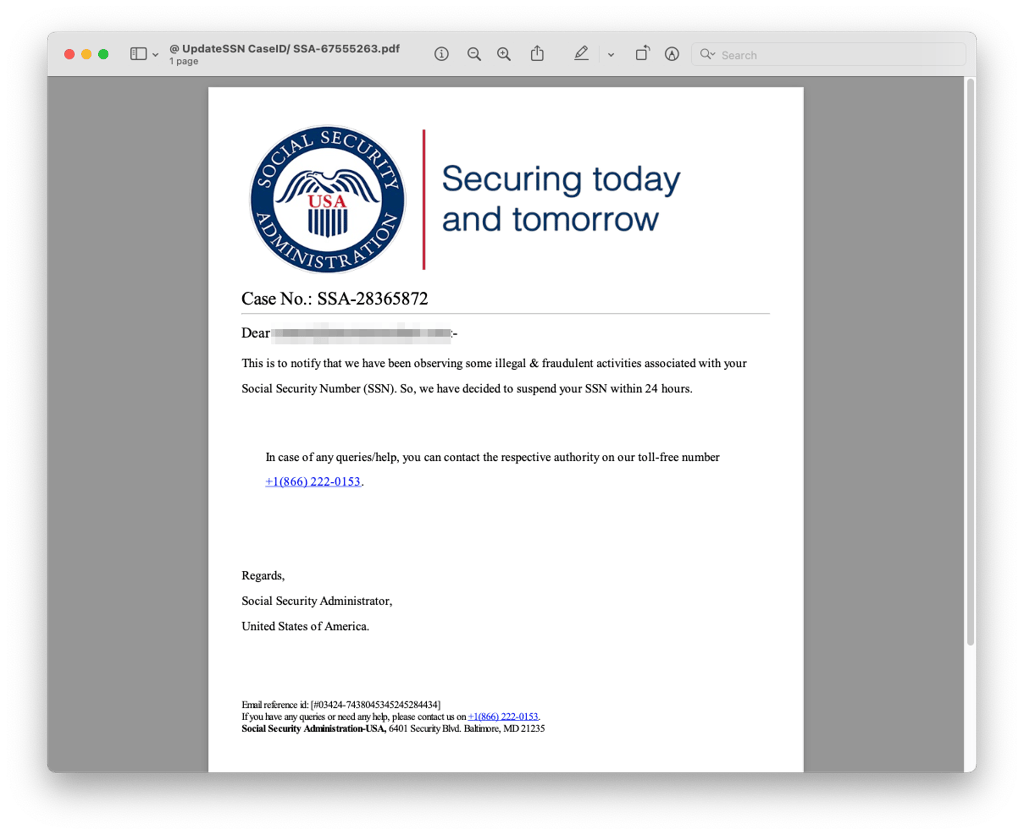
Fake messages scrutinized by INKY revealed the typical telltale lures – notifications stressing the urgency of a fabricated situation to encourage victims to respond without thinking. One cited example was the email message title that read “Fraudulent activity detected in your SSN Account” complete with a ‘case docket’ or ID number to make the scam more convincing.
The magic number
Invented in 1936 to track the eligibility for benefit payments of US citizens, SSNs have become virtual ID cards in their own right, as they are “a universal identifier linked to much more than just earnings history.”
As such, a phishing email with the tagline “your SSN is going to be suspended” can carry a lot of weight, especially with a citizen dependent on state payments or an immigrant worker yet unfamiliar with the US system.
“Note the element of urgency in some of these subject lines,” said INKY. “Urgency is a phisher’s best friend. It causes people to panic and make ill-considered decisions.”
The PDF letters sent by the phishing scammers feature the SSA’s branded logo, but not all aspects of the fake communication were so convincing. As is often the case with such attacks, frequently launched from abroad where the target country’s native language is not spoken fluently, grammatical errors gave scammers away – but only, of course, if a victim is sufficiently sharp-eyed and has a good grasp of English themselves.
The vishing aspect of the campaign entailed duping the victim into calling a fake number – instead of speaking with an SSA employee, they would end up giving their SSN to a cybercriminal at the other end of the line.
“Vishing is a type of cybercrime that uses the telephone to steal confidential information,” said INKY. “In this instance, the phone number provided in the letter does not belong to the SSA. When called, phishers answering ask their victims to confirm their SSN so it can be unsuspended. In some instances they will even claim that a new one has been issued for a fee.”
How to protect yourself
INKY urges temporary and permanent residents in the US who regularly use email to always check the URL of any link they receive – in this case, doing so would have revealed a random Gmail address that had nothing to do with the SSA.
Doing a bit of background research on key government organizations can also help to thwart digital con artists. “The SSA uses physical letters to communicate problems,” said INKY. “They only contact people if they have ongoing business with them [and] will never threaten to suspend an SSN or demand payment via cash, gift card, prepaid debit card, cryptocurrency, or wire transfer.”
INKY also pointed out that the SSA never requests personal or banking information in an email, during a phone call, or via an online service.
“Preying upon our greatest worries can be a successful tactic when it comes to cybercrime,” INKY added. “Thankfully, one of the best remedies for worry is preparation.”






Your email address will not be published. Required fields are markedmarked