
The notorious threat group ALPHV/BlackCat claims they’ve “unseized” their own dark website – only hours after the FBI boasted they had taken it down.
The ransomware world exploded with drama Tuesday as the cat and mouse game between the FBI and the ALPHV/BlackCat ransomware group continues to unfold.
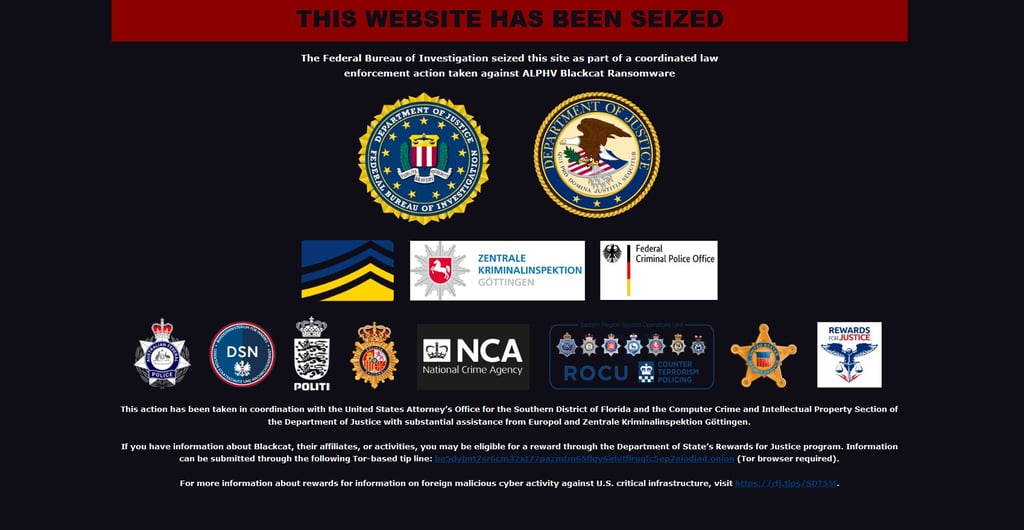
After a week of speculation, the US Federal Bureau of Investigations (FBI) announced Tuesday morning, December 19th, it had seized the ransom gang’s dark web blog.
But the group seems to have resurrected – if it was ever in danger of being taken down – and announced it had taken back control of its own web domain.
“THIS WEBSITE HAS BEEN UNSEIZED,“ it posted on what appears to be a different onion address than the FBI’s.
The group telling its fans “Ladies & Gentlemen! We've moved here,” along with yet another fresh onion address.
Note that Cybernews was unable to connect to the ALPHV/BlackCat servers at its new given address, but malware researchers at vx-underground posted a screenshot of the group’s claim on X.
What’s more, as backlash for the FBI’s actions, the group also announced that its rules of engagement have officially changed, and it will now allow other hacker groups to use its ransomware variant to target US critical infrastructure, which it forbade in the past.
The ALPHV/BlackCat onion site had mysteriously disappeared in early December, prompting speculation among the online community (both good and bad) that either law enforcement had caught up with the hacker group or the removal was part of a planned rebrand.
"In the aftermath of such large-scale law enforcement disruptions, uncertainty often permeates criminal organizations," said Michael McPherson, Senior Vice President of Technical Operations at ReliaQuest.
McPherson – also a former FBI special agent – explained that “in previous similar cases, the targeting of a ransomware group has typically resulted in operations ceasing, before members moved to other ransomware programs, or formed new groups.”
“However, as noteworthy as this disruption is, there is no mention of any corresponding arrests,” he said.
Earlier Tuesday the group reached out to vx-underground, who had been posting updates on the saga, to dispel any rumors.
"ALPHV ransomware group administrative group has contacted us to inform us they have moved their servers and blogs," vx-underground posted on X.
The group, known for "setting the record straight in its web postings," also wrote out a lengthy message to its followers explaining in detail their own version of what events took place leading up to their so-called reversal of fortune.
Critical infrastructure now fair game
"As you all know, the FBI received the keys to our blog, now we will tell you how it all happened, " ALPHV/BlackCat wrote on its "unseized" leak site, translated from Russian.
The group claims the FBI gained access to one of their multiple domain controllers (DC), possibly by hacking or working with the DC hosts.
The gang said the FBI was also able to get its hands on the decryption keys for about 400 companies, leaving another 3000 companies in the lurch.
On the new set of rules, the group explained “You can now block hospitals, nuclear power plants, anything, anywhere.”
One exception was given, “you cannot touch the CIS,” it said, referring to the Commonwealth of Independent States, the regional intergovernmental agency created after the dissolution of the Soviet Union in 1991 to support economic and security matters between its eleven-nation members; Armenia, Azerbaijan, Belarus, Kazakhstan, Kirghizstan, Moldavia, Uzbekistan, Russia, Tajikistan, Turkmenistan, and Ukraine.
“Advertisers” (hackers who use the gang’s ransom tools as a service) will now get to keep 90% of a paid ransom demand, with VIP’s getting their own designated domain controller.
“Thank you for your experience, we will take into account our mistakes and work even harder, we are waiting for your whining in chats and requests for discounts that no longer exist.” the group concluded its message.
In the meantime, Tuesday's advisory from the FBI and the US Cybersecurity Infrastructure and Security Agency(CISA) claiming to have "hacked the hackers" spoke about the gang's many affiliates and their extensive networks, experience, and data extortion operations.
"FBI investigations, as of September 2023, place the number of compromised entities at over 1000 – over half of which are in the US and approximately 250 outside the US," the release said.“
According to the US Department of Justice, the decryption keys given to ALPHV/BlackCat victims worldwide have allowed hundreds of businesses and schools to reopen, and health care and emergency services to come back online.
The FBI and CISA have not addressed ALPHV/BlackCat's most recent claims at the time of this report.
Who is ALPHV/BlackCat?
"ALPHV is one of the more prominent ransomware groups in operation,” said McPherson.
First observed in 2021, ALPHV/BlackCat is known to operate as a ransomware-as-a-service (RaaS) model by selling malware subscriptions to criminals.
The Russian-linked gang was tracked by ReliaQuest as the third most active ransomware cartel operating in Q3 2023 carrying out hundreds of attacks and causing an estimated loss of over $1 billion alone in 2023.
Known for its triple-extortion tactics, the gang was responsible for the September ransomware attacks on the Las Vegas casino giants MGM Resorts, as well as Caesars International, who is rumored to have paid a $15 million ransom to keep operations running.
McPherson said the biggest impact of a potential permanent removal of ALPHV is most likely only a short-term, albeit significant, disruption to the global ransomware scene.
“This is, unfortunately, a common outcome following law enforcement operation, reflecting the ongoing game of Whac-A-Mole in law enforcement attempting to provide a meaningful impact against this pernicious form of cybercrime,” McPherson said.
More from Cybernews:
TOC label:TOC id: #
FBI seizes ALPHV ransomware gang‘s dark web blog
Sony's Insomniac games leaked by Rhysida ransom gang
Beware: someone’s trying to log in to your Facebook account
Hotels targeted with “inhospitality” campaign
Breach of Comcast’s Xfinity exposes nearly 36 million people
Subscribe to our newsletter






Your email address will not be published. Required fields are markedmarked