
A leading electrical engineering company in Russia, Elevel, has exposed its customers' personally identifiable information (PII,) including full names and addresses.
Founded in 1991, Elevel (previously Eleko) positions itself as the leading Russian electrical engineering company that runs both an e-commerce business and wholesale stores.
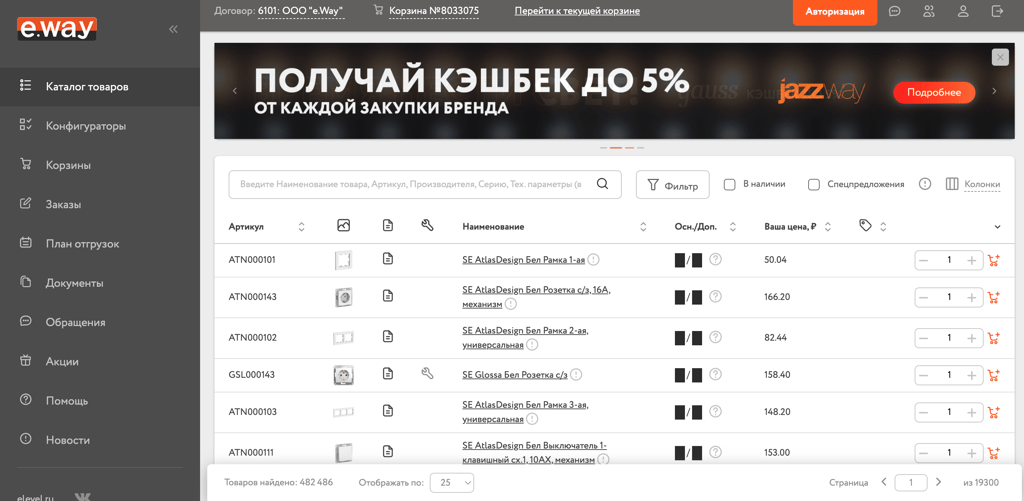
On January 24, the Cybernews research team discovered an open dataset with 1.1TB of data and attributed it to e.way – an Elevel-owned online shop with 25,000 monthly visitors.
The dataset with seven million data entries leaked two years' worth of sensitive data, including names, surnames, phone numbers, email addresses, and delivery addresses of customers.
"If left exposed, threat actors could download and clone the cluster's data and use it for nefarious purposes, including phishing attacks, as they possess sufficient PII and to make their scam seem legitimate," Cybernews researchers said.
Moreover, it contained login data and passwords in URL encoding, which is considered a relatively weak protection mechanism since it can be decoded easily.


"As a number of usernames and passwords are exposed, it could enable threat actors with valid credentials to gain further sensitive data and to impersonate users to make fraudulent purchases," Cybernews researchers noted.
The dataset is now closed. We are still waiting to receive the company's official response.
Leaky databases
We stumble upon unprotected databases daily. In some cases, they contain public data and therefore don't pose serious risks to a company or its customers.
However, that is not always the case. Recently, we broke the news about retail and gas giant, Circle K, exposing its US customers. The company left clients’ partial payment cards, complete loyalty card data, and sensitive employee information exposed to the public.
A comprehensive Cybernews research of thousands of Android apps revealed that sensitive secrets, such as open Firebase datasets or Google Storage buckets, among other things, are often hardcoded into the client side of the app. This means that threat actors can get their hands on a treasure trove of data simply by analyzing public data with the help of relatively mediocre infrastructure.
In some cases, open databases even leave companies dealing with ransomware. In one such incident, we saw a Harvard Business Publishing licensee in Turkey being threatened by crooks. The threat actor found an open dataset with 152,000 customer records, encrypted the information, and left a ransom note, threatening to leak the data and inform authorities of the EU's General Data Protection Regulation (GDPR) violations.
The Thomson Reuters leak, recently discovered by the Cybernews research team, is a stellar example of the fact that even big market players with strong preventative measures in place can be prone to similar errors.






Your email address will not be published. Required fields are markedmarked