
Russia is further pressuring Ukraine with its multi-pronged hybrid technology approach and ever more intense cyberattacks, Microsoft says. The company adds it will help Kyiv and its allies prepare for Moscow’s operations.
Winter has been tough for millions of Ukrainians as Russia continues to attack critical energy infrastructure in order to freeze the country into submission.
The cyber front has been busy as well, Microsoft says in a new report – cyberthreat actors affiliated with Russian military intelligence (GRU) have launched destructive wiper attacks against Ukraine’s networks of critical importance.
According to the report, the world should be prepared for several lines of potential Russian attacks in the digital domain this winter. First, the cyber offensive against critical infrastructure will continue, possibly also spilling over to neighboring countries such as Poland.
Second, cyber-enabled influence operations that would target other European countries are probable – Russia is constantly trying to exploit cracks in popular support for Ukraine.
Microsoft says recent missile strikes have been accompanied by cyberattacks on the same sectors. A threat group named IRIDIUM is mostly at fault here – again, it’s been associated with the GRU.
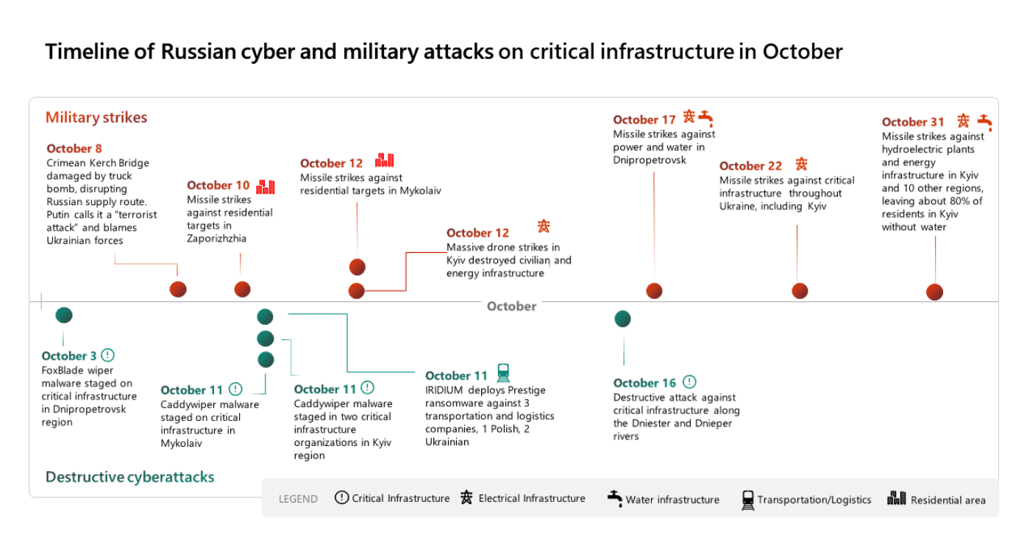
IRIDIUM has targeted Ukraine many times in the past, most notably in 2015 and 2016, when wintertime operations cut power to hundreds of thousands of citizens. The threat actor has been very active again this year, especially in October, when wiper activity spiked, and IRIDIUM deployed malware such as CaddyWiper.
Wiper malware is defined as a malicious program that seeks to erase or destroy all data kept on a computer's hard disk. In Ukraine, wipers have been targeting critical services networks, transportation, and logistics companies.
In October, Russian cyber strikes also extended outside Ukraine, when IRIDIUM deployed its novel Prestige ransomware against several logistics and transportation sector networks in Ukraine. This was the first war-related cyberattack against entities outside of Ukraine since the Viasat attack at the beginning of the invasion.
“Russian military operators also expanded destructive cyberactivity outside Ukraine to Poland, a critical logistics hub, in a possible attempt to disrupt the movement of weapons and supplies to the front,” Clint Watts, General Manager at Microsoft’s Digital Threat Analysis Center, said.
According to Watts, IRIDIUM’s success in the Prestige destructive attack was limited. Early customer notifications and rapid response, including from Microsoft’s Detection and Response Team (DART) and the Microsoft Threat Intelligence Center (MSTIC), along with local incident responders in Poland, reportedly helped contain the attack’s impact to less than 20% of one targeted organization’s network.
However, while the destructive impact was limited, IRIDIUM almost certainly collected intelligence on supply routes and logistics operations that could facilitate future attacks.
Microsoft has been among the tech giants who stepped in to back Ukraine during Russia’s invasion. It disbursed digital infrastructure into the public cloud, hence supporting critical Ukrainian services through data centers across Europe.
At the beginning of November, the company announced it would provide Kyiv with additional technology aid of around $100 million. The overall support package already exceeds $400 million.
In June 2022, Microsoft released a report, Defending Ukraine: Early Lessons from the Cyber War, where it offered a methodology for combating digital threats. The approach is built around “Four Ds” as the company is seeking to detect, disrupt, defend against and deter malicious cyber activities.






Your email address will not be published. Required fields are markedmarked